May 2003, Issue 90 Published by Linux Journal
Front Page | Back Issues | FAQ | MirrorsThe Answer Gang knowledge base (your Linux questions here!)
Search (www.linuxgazette.com)

Editor: Michael Orr
Technical Editor: Heather Stern
Senior Contributing Editor: Jim Dennis
Contributing Editors: Ben Okopnik, Dan Wilder, Don Marti
![[tm]](../gx/tm.gif) ,
http://www.linuxgazette.com/
,
http://www.linuxgazette.com/
|
...making Linux just a little more fun! |
From The Readers of Linux Gazette |
 Linux aol dial-up
Linux aol dial-upI have Peng client connect to AOL on RedHat 9.0. It connects to AOL alright but my system doesn't recognise the active connection. For my browser or gFTP clients do not connect to any http or ftp sites.
What do I have to do so that the system/n/w config understands the active connection
-Narendra
Well folks, it's not a late edition of a Fool's Day joke .. Peng really is intended for letting people use their AOL dialup to get what we'd consider more ordinary connectivity. Anyone out there hitting the net this way? Let us know how you do it! -- Heather
 Linux Infrared
Linux InfraredHi all, I am interested to make an infrared remote for linux. I have also visited the LIRC webpage. if there is any body who has already build this remote please tell me how it is working and a little bit about the circuit & driver ,library etc u have used. please share ur experience with me.
If some one is using creative infrasuite remote (credit card size) , please let me know. does it need the separate IR receiver or the inbuilt IR in the CD Rom is enough ? I have the Panasonic Tv remote at home. so please let me know too if there is any body using this remote with LIRC.
thanks in advanced.
 On a slower computer...
On a slower computer...Hello,
About 8.0 LInux installation either "stand alone"? or install with windows on a pc. can you offer tips on installing it to a 75 mhz computer. what of fdisk or other info format?
You may refer my request on to someone else in club as you desire. Thank you,for you time.
Now, small distros and distros-on-floppy we have by the dozens. But RH 8 compatible? Or kickstart floppies that chop out a bunch of that memory hogging, CPU slogging stuff? An article on keeping your Linux installers on a diet would be keen. Just in time for Summer, too. -- Heather
 A Walk through Frink's Confusion
A Walk through Frink's ConfusionI don't understand why this:
x=`echo -e "\240"`;mkdir $x;echo "hostname -f">$x/perl;chmod +x $x/perl;export PATH=$x:$PATH;clear
combined with this:
perl -we'fqdn'
is considered an Easter Egg. How do you enter it into a bash prompt to make it an Easter Egg?
Brad
*looks for riffles, JIC*
[Ben] I don't understand your question. What Easter Egg? What the heck does "enter it into a bash prompt" mean ("enter at the command line", maybe?)
That's what I meant. Woomert's command line looked as if it was meant to be entered directly into a shell prompt. Is it meant to be entered some other way?
[Ben] Ah, OK. Yes, it's meant to be entered at the shell prompt.
What did you try? What results did you get? What did you expect to see instead? Give me some info to go on, and I might be able to help you - if I can get an idea of what you're asking for.
I tried entering the x=" line, then calling perl -we'fqdn' to see the output. That worked.
[Ben] <grin> Except... it didn't. There's no such function as "fqdn" in Perl; it's just a random string that I munged up, an abbrvtn for "fully qualified domain name."
What I was expecting was something which made perl stop working or something which would munge my command line.
[Ben] That's exactly what you've got: Perl is now "broken". No matter how you invoke it, it will now type the FQDN.
I have an idea on what this is meant to do, though:
x=`echo -e "\240"`;mkdir $x;echo "hostname -f">$x/perl;chmod +x $x/perl;export PATH=$x:$PATH;clear
echo -e "\240" : ASCII code 240 mkdir $x : create a directory with name $x
[Ben] Well, with the content of $x - which is an "invisible" ASCII character (at least with the default LOCALE), easy to miss when you do an "ls".
[Jason] Hmmm....my 'ls' shows the escape character. ("\240") That's becasue the '-b' (show escape characters) is in $LS_OPTIONS, which is used in my 'ls' alias. That's pretty neat, but I find a backspace character has more intersting effects:
~/tmp$ x=$(echo -e '\b') ~/tmp$ mkdir $x ~/tmp$ touch $x/lala ~/tmp$ ls \b/ ~/tmp$ cd ^H/ ~/tmp$ ls lala ~/tmp$ cd .. ~/tmp$
It makes it look like you don't even change directory! And the output of the 'ls' command is, of course, given the -b options via my alias. Normally, (my version of) ls outputs a '?' when there's an unprintable character.
echo "hostname -f">$x/perl : echo the hostname into a file named perl in $x
[Ben] Nope. Echo the string "hostname -f" into that file.
chmod +x $x/perl : make the perl file executable
[Ben] Thus making it an executable shell script which runs "hostname -f".
export PATH=$x:PATH;clear : adds $x to the $PATH
[Ben] Much more importantly, putting $x at the front of the PATH - meaning that the executables in there will get run instead of the others. When you type "perl", the actual Perl binary never gets executed: the shell script is now the first "perl" in the path!
Is this Easter Egg supposed to make perl act strange?
[Ben] It's not an "Easter Egg"; that term has a specific meaning (hidden feature that does something cute when you run it, like the maze in MS Excel, a mini-version of a Doom-like game in Word some years ago, etc.) That's what had me confused. It's a hack (not a software hack, either; Woomert just hacked Frink's naivete, too easy of a target by half.
As to what it does - it makes Perl go away.Until Frink finds the problem and fixes it (possibly by logging out, closing that xterm, or rebooting), invoking "perl" will do nothing more than print the FQDN.
[Jason] Only in UNIX can you do so much interesting stuff with a few commands. A while back I was playing with a script that would, when run, print
rm -rf /home/username.....12345K deleted
where username is your username and 12345K is however much stuff you have in your home directory. The disk churning sounds would be 'du' running to figure out how much stuff in your home directory there was. Then the tricky bit was that the script would add some commands to your .bashrc, which changes $HOME to /tmp/$RANDOM and cds to that directory, so when the user logs in again he thinks all his files are gone. I thought about uuencoding it and posting it to the TAG on April 1st, but decided not to.
[Ben] Oh, massively cute! You should, of course, set the command prompt to show that the user is still in his home directory...))
[Jason] That's what setting $HOME does.
[Ben] Oh, I meant an explicit "/home/joe" rather than "~", but you're right - that's even better.
 Cloning workstations article
Cloning workstations articleEsteemed editor,
In your April issue of Linxu Gazette there is an an article on Cloning Workstations with Linux by Mr. Alan Ward. An article that starts with:
"Anybody who has had to install a park of 10 - 100 workstations with
exactly the same operating system and programs will have wondered if ...etc"
is able to raise my curiousity.
IMHO the best solution for a hundred or so workstations.
Kind regards,
Dirk
Please note that g4u is based on BSD, not Linux. The techniques used are, however, very similar.
Best regards,
Alan Ward
|
...making Linux just a little more fun! |
By The Readers of Linux Gazette |
 linux baby clothes?
linux baby clothes?gday - how'd it go with the inquiry about Linux baby clothes?
- How about this one here:
- http://www.thinkgeek.com/tshirts/kids
 bookmark conversion
bookmark conversionHi,
I have a www browser bookmark conversion problem (and a partial answer
![]() ). I'm currently using Opera as a browser but I wanted to also use
Konqueror. As always, there is an issue with the bookmarks: it's
difficult to "port" them. After one hour of groping and hacking I
managed to write a little script that does the opera->konqueror port.
But it is ugly and it doesn't work in the other direction.
). I'm currently using Opera as a browser but I wanted to also use
Konqueror. As always, there is an issue with the bookmarks: it's
difficult to "port" them. After one hour of groping and hacking I
managed to write a little script that does the opera->konqueror port.
But it is ugly and it doesn't work in the other direction.
Do you know of such bookmark converting apps/scripts (on linux!)? Konqueror (in kde 3.0) seems to know how to import/export bookmarks to netscape and mozilla, but not more.
I hope this qualifies as a Linux question
![]() . It's an all platform
issue, but that doesn't mean it's not linux, right ?
. It's an all platform
issue, but that doesn't mean it's not linux, right ?
![]()
I included my partial-answer-script. Maybe someone can use it
![]() . I
don't really know perl, my script is probably very ugly but it worked
for me. It's a filter, you have to use redirection and then copy the
output file to the konqueror bookmark file.
. I
don't really know perl, my script is probably very ugly but it worked
for me. It's a filter, you have to use redirection and then copy the
output file to the konqueror bookmark file.
Thanks,
Miron Brezuleanu
See attached op2konq.pl
[K.-H.] Hmm... opera has some bookmark export variants too.
Like file-export-bookmarks_as_html looks like a very much universal export format if you simply load that html page and klick on the bookmark you want.
As I remember netscape bookmarks are a simple html layout as well which you can directly load as an html-page.
 Cups
CupsThis is a multi-part message in MIME format.
------=_NextPart_000_0030_01C2FDD5.E597FE00 Content-Type: text/plain;
charset="iso-8859-1" Content-Transfer-Encoding: quoted-printable
I'm sure you're unaware of this, but you sent your message with extraneous MIME headers like the foregoing, and with your entire message printed a second time in HTML. Please change your mailer's settings to stop it from doing this. Instructions are here: http://expita.com/nomime.html#outlook5
For more information, please see (http://www.linuxgazette.com/tag/ask-the-gang.html#non_text)
Normally I leave this part out. However, since I note that Rick has had to utter this little macro an awful lot of times this month, I figured I'd help a few souls out there by seeing it get mentioned. The answer in this case is tiny - so this brings it up to a whole Two Cents worth :D -- Heather
How do you set printing priorities with cups?
Using the -p option:
$ /usr/bin/lp -d LaserJet -p 90 foo
...gives the job of printing file foo a priority of 90 out of 100. Default priority level is 50.
 DOS functions in Linux' gcc?
DOS functions in Linux' gcc?Respected sir/ madam ,
can i use execute interrupt 11h and 13 h as i can use in TURBO C using int86 function , plz give some inforamtion or notes how to do that in linux using gcc thanking you in advance
I'm not sure if it's possible in the same way it is in DOS, but it's definitely not the done thing. Wine (http://www.winehq.com) has code in its DOS emulation dll, which you could probably use in a similar way. Look in wine/msdos/ and wine/dlls/winedos
Int 11 is equipment check and 13 is disk services, right? For int 11, you might try using Discover (http://www.progeny.com/products/discover). For int 13, you'd need to be more specific
 Internet by call in USA?
Internet by call in USA?In response to Help Wanted #6, Issue 89. -- Heather
Hi matthi
In US, visit the next public library - there are some PCs in every public library with which you can access internet (and therefore via webmailer your mail) for free. Also, many Hotels/Motels have free web-access by LAN or, al least, an PC with freee webaccess (motels with moderate prices too, afaik motel 8, motel 6) - you can choose your accomodation by that.
 [GL] nis problem
[GL] nis problemThe author here - a member of the GLUE list, contacts for "Groups of Linux Users Everywhere" - was really hoping he was wrong, but this is how the dreaded YP stuff really works. A tip for all who have to deal with NIS. -- Heather
1) I search various web-sites, but I cann't find this.my nis-server and nis-client works properly. ypbind at client detects the nis-server also. yp.conf,network files all r fully configured in client and server both. "ypcat passwd" also displays the user info in both client & server. But when I create any new user at nis-server,I can get user-info by running "ypcat passwd" only when then I execute make command in /var/yp or "ypinit -m" in /lib/usr/yp folder AGAIN.I want to know that IS it Required to execute MAKE COMMAND AGAIN & AGAIN When any New User Created ?
In a word, yes.
 Pctel hsp micromodem 56 config.........RedHat 8.0
Pctel hsp micromodem 56 config.........RedHat 8.0Hi there,
I wonder if this would be useful to some of you out there.I had some problems configuring my Pctel PCI modem.After a lot of searching I found a driver at linmodems.org.The compilation went on perfectly but when I tried to load the modules with insmod I could not load the modules and it would display that the module is compiled with GCC 3 and hence cannot be loaded.
[Kapil] Thanks for your hints ...
Note that many distro kernels are compiled with gcc 2.95 (in fact I don't believe I have successfully compiled a kernel with gcc >= 3.0).
Thus a possibly better solution is to install gcc-2.95 and compile kernel modules using that.
An alternative is to re-compile your kernel with gcc 3 and then you can use modules compiled with gcc 3 as well.
If you are facing the same problem do this....
1.At the console type
insmod -f pctel insmod -f ptserial
(instructions on installing the modules can be found in the readme file found with the package). (If you are using the same tarball from linmodems.org i.e.,pctel-0.9.6.tar.gz you have to type commands as it is). You will see some messages but it does not matter much.
[Kapil] Generally speaking, I would do an "insmod -f" only if I was in a hurry or if I couldn't even boot-to-fix witout it. But it should never be allowed to be a "permanent" solution.
2.If you are using KPPP to connect to the internet do this..... create a new connection,fill in the connection details and other things. Then go to the modem tab and click on modem commands.In the section named initialization string 2 give the following "AT&FX1&C1" and press ok.
3.Instead of loading the modules each time the above given commands you create a script which you can execute before starting kppp. I can't assure that it is going to work,but you might as well give it a try.
Hope this will help. Vivek.
[Kapil] Me too.
 Debian upgrade howto
Debian upgrade howtohow to upgrade the existing debian version without reinstalling ? (for an ex. potato to woody)
Debian's built-in upgrade process is controlled by the /etc/apt/sources.list file and by the apt-get package-retrieval utility. sources.list specifies where to look for new packages (Web or ftp sites, CD-ROMs, hard drive directories, etc.), and apt-get fetches both available-package catalogues and the packages themselves. Your sources.list probably looks like this:
deb http://http.us.debian.org/debian stable main non-free contrib
deb http://non-us.debian.org/debian-non-US stable/non-US main contrib non-free
deb http://security.debian.org stable/updates main contrib non-free
Notice the word "stable". At the time you installed Debian, "stable" referred to 2.2/potato. These days, "stable" has progressed to 3.0/woody: The alias name "oldstable" can still be used to refer to potato, or you can just use the name potato.
That is, if the machine you're talking about has Internet access, you can upgrade in two stages, like this.
1. Edit sources.list to refer to "potato" by name:
deb http://http.us.debian.org/debian potato main non-free contrib
deb http://non-us.debian.org/debian-non-US potato/non-US main contrib non-free
deb http://security.debian.org potato/updates main contrib non-free
As root, retrieve the latest available-packages list for potato:
# apt-get update
Now, upgrade all installed packages to the latest for the potato series:
# apt-get dist-upgrade
2. Re-edit sources.list to refer to "stable" (which is now 3.0/woody):
deb http://http.us.debian.org/debian stable main non-free contrib deb http://non-us.debian.org/debian-non-US stable/non-US main contrib non-free deb http://security.debian.org stable/updates main contrib non-free
# apt-get update
# apt-get dist-upgrade
The point of doing the upgrade in two stages is to avoid introducing dramatic version differences, all at once.
However, it may be that pulling down a hundred or so packages from the Internet isn't practical. If so, you can acquire a set of Official Debian 3.0r1 CD-ROMs. The full set is 7 CDs. (You don't need to get all seven, if you don't want to.) To register them in sources.list, first comment out any existing "deb" lines in that file, and then run the apt-cdrom utility once for each CD. Then:
# apt-get update
# apt-get dist-upgrade
That's just about all there is to it. Make sure you take note of any warnings or advisories shown to you during the upgrade process.
I was looking for this a long. and U have given me the solution.
I know that "thanks a lot" is not enough. any how wish u my best wishes -
![]() ))
))
 more verbose and useful assert()
more verbose and useful assert()In reference to the assert() macro that good programmers use to catch bugs that should be fixed before the user sees them -
Unfortunately, when a programmer debugs somebody else's code, an assert failure may be rather difficult to interpret. What does assert(p == NULL); failure mean? You will not know until you look at the source code at that point and try to understand what's going on. But what if the assert was changed to:
assert (p == NULL && "Please deallocate your GC handle before allocating a new one");
Now the programmer can read the message, which will be printed along with the rest of the stuff in the assert, smack himself on the forehead and shout "doh. I know where the problem is!" The assert works because the string pointer is always non-zero and if p == NULL, will not cause the assert to fail.
This seems pretty obvious, now that I have figured it out, but I have never seen this technique used in any piece of code. The effect can be achieved by using a custom assert library, but why introduce a dependency when you don't have to?
[Jimmy O'Regan] Would it not be better to use
if (!assert (p == NULL))
fprintf (stderr, "Please deallocate your GC handle before allocating a new one");
[Didier Heyden] Nope; assert() actually aborts the program if its argument is 'false.' This means that your own message would never be printed, even if the 'p' variable were NULL. Instead, you'd see something like:
PROGNAME: SOURCE.c:31415: FUNCTION: Assertion `p == NULL' failed. Aborted
then the program would terminate (and possibly dump core).
OTOH, with Mike's method you'd get a message similar to:
PROGNAME: SOURCE.c:27182: FUNCTION: Assertion `p == NULL && "Please deallocate your GC handle..."' failed. Aborted
The reason his solution works is that a string constant in C (even an "empty" one) always evaluates as a 'true' condition (a non-null memory reference indeed).
Another advantage of sticking with "simple" assert() macro calls is that you can disable all of them at once, merely by #defining the NDEBUG macro at compilation time. In that case, all assert() instructions will expand to nothing at all.
[Jimmy] (or similar, apologies for my rusty C)
[Didier] Naaah.I wish I could remember the specific syntactical issues of my own rusty programming languages as precisely as you do. Expect my over-volatile memory to bring back sooner or later awful games of 2^^7 errors such as
#/usr/bin/perl -W
using strict;
my despair = {'Why', 'the heck', 'doesn't this', 'work'}
for each (@cry in $despair) { echo @cry, " (sob) " }
(Don't laugh: it's based on countless true stories).
 carrier errors
carrier errorsI came across your "Answer guy" site while searching for info on ifconfig errors. Unfortunately, it did not help with my problem, but since you provide an e-mail link, I'm not too proud to ask.
The question I'm trying to understand is "what are "carrier" errors. I'm getting "carrier" errors on 100% of my my TX packets and can't connect to the rest of the network, but the man pages for ifconfig don't tell me what the errors are and I'm at a loss so far to find information on this.
Carrier errors is jargonese for Cable fault. Please check the cable you are using (try a different one if you have one). Of course it could also be a loose contact problem.
Carrier = Signal Carrier = standing wave on which signals are transmitted using "modulation". That's about as much as I remember from by College course in Electronics.
The complete problem is that I'm running both WinXP and Linux (Knoppix booted from CD) on an HP notebook. Knoppix used to boot and connect to the network fine, but now it has stopped working! I'm running strictly from CD, no install or configuration information on my system, just the normal Knoppix auto- configuration that worked fine on the hardware before, yet now for reasons unknown I get these carrier errors and can not transmit anything on the network (sniffing the wire confirms that nothing is going out). Obviously I can no longer get my network settings with DHCP (which also used to work fine on my local network for this computer), but I cannot manually configure the card to work either. Do you have any insight to what might cause this?
Thanks. Unfortunately, in this case the "carrier errors" are not cable errors. Here are the details that confirm this:
The hardware works 100% correctly under WinXP, including sniffing the
cable and seeing absolutely no errors in a large number of packets.
The hardware used to work under Linux (Knoppix booted from CD) but no longer does, even with the very same bootable CD. There are no packets getting out onto the cable at all, again confirmed by sniffing the cable.
A completely different cable was also used to route the notebook computer to a separate hub where the packets could be watched by another computer. Still no packets were on the wire.
I wrote earlier: Carrier = Signal Carrier = standing wave ...
So at least I feel partially vindicated. There is no standing wave hence no signal
Apparently other Linux issues can manifest themselves as carrier errors, but I have not yet been able to determine what counts as a carrier error in Linux.
Let's apply Occam's razor here based on the fact the "it used to work with the same Knoppix CD". What could have changed?
- Not the CD. And hence not Linux or the software that comes with it.
- Not the cable (this has been checked by you).
- Not the hardware (it works under that other OS so its not critically damaged).
Thus the problem has to be with the remaining "soft" component. That is BIOS/flash settings. Some Network cards store some settings. You could examine these settings using the mii-tools. Additionally, check whether you have made some changes to the BIOS.
I just wanted to give you some feedback. Thanks very much for the reference to mii-rtools, it really helped. It looks almost certain at this point that Microsoft's "security updates" are changing NIC configuration eeproms. And, of course, Microsoft knows not to use the bad configuration and works fine with the change, but another OS like Linux that trusts that the configuration in the eeprom is what the manufacturer or user wants fails. I've found several other users that have been trying to figure out what happened, why their CD used to work fine but now fails on the same system. We all accepted Microsoft "security updates". We are now trying to get a test done with some networking tools that can watch the content of the eeprom and catch when it changes, so I expect to have evidence to support this soon.
I'm pretty sure it can - I know a dyed-in-the-wool linuxer who currently has to consider his happy little Orinoco family wireless pcmcia card a piece of junk because a "helpful" Microsoft update has put it into a state that Linux and BSD tools don't seem to be able to get it out of. Of course it works fone in the other OS. Grrr. -- Heather
 architecture
architectureI have seen that different linux architecture are present based on different processor architecture. like i386, i586, i686 etc. what are these & how to know the architecture of my processor ?
JK, Linux provides an excellent facility for this sort of thing, in the form of /proc/cpuinfo. Here's the one from the server I'm mailing this from:
For those ignorant of or who simply are happy to avoid the text editor vi (or its friendlier cousin vim) :r is a command which, when issued from command mode, will read what comes after it. :r! runs a command, which can be nice for inhaling man page fragments, too. Making this a Three Cent Tip... -- Heather
:r /proc/cpuinfo processor : 0 vendor_id : GenuineIntel cpu family : 6 model : 7 model name : Pentium III (Katmai) stepping : 2 cpu MHz : 498.755 cache size : 512 KB fdiv_bug : no hlt_bug : no f00f_bug : no coma_bug : no fpu : yes fpu_exception : yes cpuid level : 2 wp : yes flags : fpu vme de pse tsc msr pae mce cx8 apic sep mtrr pge mca cmov pat pse36 mmx fxsr sse bogomips : 996.14
There. More than you really wanted to know about the host's CPU. Of course, the above gives information about the hardware. The machine's kernel may or may not have been compiled with appropriate optimistions, though that will generally be included in the output of uname -r (kernel release).
[Pradeep] i386, i586, i686 are different kind of processor architectures developed by intel. The following link has some info about this: http://www.rebourne.org/chiparch.htm
In the terminology of the hardware hackers, these are considered the same architecture (32 bit Intel, "i386" if you're looking in the kernel source tree). There are a few optimizations, but the way they think is similar. Contrast a Sparc, a Strongarm (found in many handhelds), or even Intel's own ia64 ("Itanium" if you prefer them by name). -- Heather
 floppy woes
floppy woesI'm running SuSE 7.1 and Win98 on separate hard drives in a 900 Mhz Celeron machine. Things were working fine until recently, when I could no longer access my floppy while in SuSE. The same drive reads and writes perfectly in Win98. When attempting to mount the floppy either by clicking the desktop icon, or by typing the command in the terminal, I receive the error '/dev/fd0 is not a block device'. What could have happened to cause this, and what can I do to repair it?
Some possibilities suggest themselves.
- The device node is not properly created. Run 'ls -l /dev/fd0' and check.
- You have a modular floppy driver which is not loaded. Run '/sbin/lsmod' to check whether the driver is loaded.
[Didier Heyden] A third possibility is that your floppy disks and/or drive are actually defective. A 'mount' command issued on /dev/fd0 (assuming that this block device file and the kernel modules are all set up properly) will first try to access the disk's boot sector. If any I/O error occurs then, the 'mount' will fail with the error message you mention.
Take a look at the system log files (usually /var/log/messages, but you can also use the 'dmesg' command). Check whether errors like
[...] kernel: end_request: I/O error, dev 02:00 (floppy), sector 0
are present; if so, try to mount a few other floppy disks. If the system keeps producing an error similar to the above, chances are that you will have to replace your floppy drive very soon -- in particular if the very same diskettes are correctly mounted and read on some other (Linux) box.
There was a time when such a problem could be caused by a drive head "misalignment", but I'm not sure it's still the case these days.
I think it can be; also, depending on your console setup, you might not have to dig in the logs to see these complaints, as they might spew on your console rather vocally.
First thing I'd check is whetehr there's a file in your /dev/ area that used to be your floppy node, fd0 or any of the others starting with fd. -- Heather
I don't know much about WinXX, though I guess that that other OS either does more retries before giving up or is too lax regarding sanity checks prior to granting access to the user (I can't help favoring the latter explanation).
 firewalls
firewallsOn Wed, 9 Apr 2003 13:48:45 +0100 (BST), deepa lakshmi wrote:
hello
Hi,
i have a firewall machine .i also have a machine with ip 192.168.1.7 behind the firewall.
i added prerouting rules to forward incoming request to internal web servers which are behind firewall.
now i want machine with ip 192.168.1.7 to have internet access through firewall. i have tried with this rules.but no resonse fron machine rules are
-A POSTROUTING -o eth0 -j SNAT --to-source 202.54.100.54 -A FORWARD -i eth1 -j ACCEPT -A FORWARD -m state --state ESTABLISHED,RELATED -j ACCEPT
but it's not working.
before saying that. Since we have no means to guess what actually happens on your system when you try the firewall rules you mention, you cannot expect us to be able to provide much help in exchange for so little information as you've given.
For example, is the above ruleset complete, or is it (as is more likely) only a subset of the actual rules you're using? Are these rules accepted at all when you enter them on the command line? What do the log files on your firewall machine say? Did you try a packet sniffer such as "tcpdump" or "ethereal" on its network interfaces? Did you make sure all required kernel modules have been compiled, installed and are actually loaded? Is "IPv4 forwarding" enabled? etc, etc.
I'm not an "iptables" expert myself, but I think the "-t <table>" option is not an unimportant one.
Here's a precious resource about setting up a Netfilter/iptables firewall. It covers pretty much everything (including source NAT and masquerading) and has a number of useful examples:
http://iptables-tutorial.frozentux.net/iptables-tutorial.html
<solemnly>
Beware that in order to set up a firewall in the Right Way, you
must definitely know what you're doing. Help yourself. Googlesearch.
Read howtos, tutorials and examples; once you have understood them,
give them a try. Observe the results carefully. Then -- only then --
ask a precise question.
![]() </solemnly>
</solemnly>
[Jason Creighton] Well, a problem I see is that for the SNAT rule, you need to specify the table, like this:
-t nat -A POSTROUTING -o eth0 -j SNAT --to-source 202.54.100.54
All the NAT rules go in the (guess what?) "nat" table. The default table is 'filter', which is used when no table is specified.
 Internet Cafe ?
Internet Cafe ?Wally Bannon wrote:
I have a client who is Aboriginal here in Northern ontario looking to
set up a Internet Cafe. There are no location in the city of Thunder Bay.
Can you direct me to where I can get info on " how to set up or
establish an Internet Cafe"
This person is a youth age 25 who can access Gov't funding for
assistance to capitalize the project
If you want to use some combination of both Linux and Windows clients controlled by a Linux server, try Zeiberbude:
http://zeiberbude.sourceforge.net
If you want Linux clients connecting to a Linux server, you could also try DireqCafe:
http://akinimod.sourceforge.net/icafereal.html
This is built for the Linux Terminal Server project:
http://www.ltsp.org
If you want Windows clients connecting to a Linux server, try Prepaid Accounting:
http://quozl.netrek.org/ppa
If you want Windows clients connecting to a Windows server, you'll have to try asking somewhere else.
[Faber Fedor] If you go to www.google.com and type in "internet cafe howto" the first link is back to us -- http://www.linuxgazette.com/issue70/tag/9.html ! There are several other good links mentioned there on google.
 Making IPTABLES complain...
Making IPTABLES complain...I have a little question. I have a iptables rule set that works perfectly. The problem is that to check if it is working as it has to I have to check the long log files every some time.
I really would like my laptop to complain when some unauthorized conection is attempted in real time or when my laptop tries to connect to other host without me doing it. Much the way Zonealarm complains. I just want the system to tell me that something strange is going on without me having to see the logfiles all the time or installing a dedicated IDS (snort).
I think if I can get iptables to send all the dropped packets somewhere a normal user (not root) can read them, I can grab that data periodically and display a little alarm with it using maybe karamba?? Any sugestions??
Just a little personal firewall for my desktop, since linux is becoming a candidate for personal desktop (It is already for me) this feature would be a good add-on.
[Jason] Now, do you want the data that the packets contain, or just the packet headers? The LOG target, will, as you know (if you're reading log files) give that information. If you really need the data, look into the ULOG target. The ULOG target sends the packet through a netlink socket to any listening process in userspace, so you'll need a daemon running to "catch" all those packets. Search the web for "iptables ULOG target", I haven't done much research into that method, so I don't know how well it would work.
It sounds like you want a pop-up window every time somebody sends you a packet that iptables drops. That's tricky to implement. Here's a half-way solution:
tail -f /var/log/syslog | perl -ne 'print "\a$1\n" if (/.*?firewall: *(.*)/)'
Assuming you have the --log-prefix option that's given to the LOG target set to 'firewall:' and that the kernel messages are ending up in /var/log/syslog, this will beep and print the packet details whenever a dropped packet comes in. You could then leave this running in a terminal. You might also want to have the 'limit' match on your logging rule, for two reasons:
- Somebody who knows what packets you're logging would flood your logs by send lots of illegal packets.
- You don't want to be driven crazy by beeps if somebody starts port-scanning you.
There's probably some better solutions out there, but this works if all you want is the packet details. Also, it's probably overkill to have perl doing this.
[Matthias] You could configure your logging client to log your iptables log to a second file which is group writeable (e.g. group "log") and then parse this log file.
You should search for a /etc/syslog.conf or similar. If you have problems you may ask on the list how to configure your particular logging client (syslogd) on your distribution.
 iso
isoi have an iso image how do i burn it to auto run from cd
[Rick] You use cdrecord.
Yes, cdrecord is available for Windows, albeit usually built under cygwin, so you might need the cygwin runtime libraries. We also had a considerable discussion of many avialable types of CD burning software in a past issue: Best of ISO Burning Under Windows
I've seen that there is software to soft-mount a .iso raw CD image file as a filesystem under Windows - much like the way Linux and other UNIX users can "loopback" mount them (so they look like a real disc). Search Tucows or some other MSwin software archive to find that stuff. -- Heather
its easy cd/dvd.6
[Rick] No, when you're mailing a mailing list called linux-questions-only@ssc.com, it most definitely is not Roxio Easy CD/DVD 6 for MS-Wind*ws. It's cdrecord. Get it?
Much thrashing by the gang about whether a reader can "get" that we're going to describe free software to them when they haven't really got their hands on that first Linux CD yet, snipped. Suffice it to say we support folks escaping from addiction to the Borg's sugar cubes, but if you have proprietary software, questions about it really ought to go to its paid support staff. -- Heather
[Karl-Heinz Herrman] if it is an true and real iso9660 (plus extensions like Joliet or Rockridge) yous take it and burn as it is onto a CD. That's it.
To add some guesses myself:
- That Roxio thingy is obviously a WinXX program
- "auto run" might mean boot. But then it might mean autorun, which is an inherent feature of WinXX to execute autorun.inf on inserting a CD (and the first thing I switch off if I have to put my fingers on a Winbox).
In any case -- the bootability of a CD or the autorun.inf file are either in the iso or not. If not, it won't "auto run".
 mcrypt
mcryptHave started to play around with mcrypt (my version 2.6.4) mostly to learn. It works fine, but have a Q:
Having an encrypted file on a (read only) CD, I would like to know
if there is any way to use the CD-file as input only and needed
working files directed to a normal (R/W) diskfile ?
Have tried redirection "mcrypt .... CD-file > HD-file" but mcrypt reports "read only media". Any tricks to do this ? Currently I have to copy the CD-file to a R/W-file and then decrypt it.
Well, running "strace" on "mcrypt" shows it acting like it left its brain in the dishwasher for too long: it tries (non-optionally) to write the encrypted file in the same place where the source file is - even if you issue the request from somewhere else. Duh! Plus, the "-F" switch that's supposed to make it go to STDOUT does exactly the same thing in the above case. The program is BAD (Broken As Designed.)
Here's a solution that works, though:
cat /mnt/cdrom/foo | mcrypt -F > foo.nc
Hi Ben,
Thanks a lot. I do recal your name, you have helped out lot in the past.
Your method "cat /.../foo | mcrypt .." works fine. NOTE that I am in a learning phase (as always). Are there better crypt applications around.
Thanks a lot.
Hans.
 how to config a modem to received call
how to config a modem to received calli have the problem to config my modem for received login in , i ready make the test to call out the work, but i can't do for received. becouse i tried to make a login in for internet service.
You want to have a look at sendfax and mgetty: for example at: http://www.leo.org/~doering/mgetty
mgetty is a daemon which is run by init (see /etc/init.conf for configuration). It will reply to an incoming call on a modem.
K.-H.
 mounting cd
mounting cdhi
i had problem with my unix. i would like to know how to mount cd on my system which is running redhat 7.0
thank you
1) Find out which device your CD is attached to. Try
dmesg | less
spacebar takes you forward, q to quit. Look for something in the messages about a CD. It'll probabably be attached to /dev/hdc or /dev/hdb. Unless it's something unusual like a USB or SCSI CD.
As root,
mkdir /cdrom
add a line to /etc/fstab that looks like:
/dev/hdc /cdrom iso9660 defaults,noauto,ro,user 0 0
using your favorite text editor, such as vi, emacs, nedit, kedit, pico, whatever.
If the CD is on /dev/hdd, use that in place of hdc.
As yourself, put a CD in the slot and give command
mount /cdrom
to look at files there
cd /cdrom
ls
and so on.
To unmount it,
umount /cdrom
 linux S/W ? for movies
linux S/W ? for movies[Huibert Alblas] There are some GUIs (Graphical User Interfaces available for these things too: avidemux (http://avidemux.sourceforge.net) (frontend to transcode avi->everything) DVD::RIP (http://www.exit1.org/dvdrip) (frontend for transcoding DVD->everything)
Then you are set to go:
Safest way is to demultiplex the audio and video from the 3 avi's. Then concat the 3 audio and video streams, resulting in 1 big audio and 1 big video stream.
[Ben Okopnik] I've also had good luck with "mplayer" (a wonderful all-around piece of software); just a couple of days ago, I wanted to grab the audio stream from a DVD title, so -
mplayer -dvd 12 -ao:pcm > file.wav
Of course, there's the obvious complement of "-vo" for video. For the available output formats, see
mplayer -ao help
or
mplayer -vo help
Quite an impressive list in both.
Hi all,
I have downloaded the great MPlayer & compiled it under debian. but whenever I play with
mplayer /cdrom/movie.dat
...MPlayer plays it within a very small window. maximizing the window can't change the display area. again there is a synchronization problem between the audio & video output.
[Robos] if you have xvideo support (mplayer -vo xv) try "f" during playback. Else, try -zoom and|or -fs. If you post your grafic card I can (maybe) tell you what option to use to get fullscreen.
it plays sound more quickly than the video. I have also tried with the option -autosync n (where n=1,2 etc), but result is same. could any one suggest me a solution ?
another newbie question. I have gone through the HTML doc of mencoder. still the difference between 2-pass & 3-pass method is not clear to me. *2-pass* gives better image quality. but what is the advantage of 3-pass ? is it superior to 2-pass. please let me know.
[Robos] If I understand it correctly 3 pass does mp3 separately of the video...
Anyone who has sufficient info to keep us in sync here? Maybe you could write an article for us :D -- Heather
 mouse driver, rather not
mouse driver, rather notHello,
I tried editing the makefile in the drivers/char directory by removing busmouse.o and other other mice. I then compiled the kernel and booted using the new image. The mouse was still running after the reboot.
what does this mean? Isn't gpm an application that uses the busmouse and other mice functions? Only when i kill the gpm daemon does the mouse stop functioning.
Any information would be useful to me.
[Joel Mayes] An .o file is generally an object file, it is the result of the compilation, so removing one will generally just get it remade the next time you compile.
Also the busmouse.[c|h] files are for an old style serial busmouse driver, if you have a reasonably modern PC the chances are you have either a USB or a PS2 mouse.
If you want to remove mouse support from the kernel, rather then deleting files from the kernel source, which could have interesting results (and you might want to include that support your deleting in the futher) in "menuconfig" goto "Character Devices" -> "Mice" and disable support
[Heather] Hi Joel. Ravi, there's more to this that you haven't mentioned, so I'm going to have to fill in with some guessing.
If you didn't tell your bootloader about your new kernel (even if you succeeded at chopping the mice out, instead of merely asking the build system to ignore them) ... it's probably still booting the old kernel.
Type 'uname -a' to see your running kernel version.
When you build your kernel, go into the Makefile at the top of your sources, and add a marker of your own into the EXTRAVERSION variable. That way, if you succeed at grafting your own kernel in, then you will see your marker from the uname output. Also its modules will be seperated by the extended version, so you won't chance loading the mouse support module of a kindred kernel, at least not unless you deliberately insmod it.
I do this all the time to mention a systemname when I build kernels that are only supposed to run on a specific host. Usually it's a warning that the kernel is unlikely to boot other boxen; sometimes it's a sign that I succeeded at applying a particular patch, or have a particular list of options selected.
Then type 'make menuconfig' (not just 'menuconfig') and tweak whatever things you want or not. Note that X will be useless without some serious tweaking, e.g. maybe using a windowmanager like ratpoison which is keyboard driven, and adjusting the config so it won't die without a mouse.
It may be easier to simply adjust the sysvinit setup so it does not automatically launch gpm for you. You could directly remove the gpm package so it will stop haunting you (try as root, either 'rpm -e gpm' or 'apt-get --purge remove gpm')... or modify your init sequence so that gpm is no longer automatically invoked. Note that most distros also have helper apps to set all the right things for that too - debian has update-rc.d, SuSE has YaST, Red Hat had linuxconf and may have newer and more friendly interfaces now, etc. The ultimate arbiter of what happens during your startup though, is /etc/inittab, which is really the file that init reads when it gets started. All the other stuff is just following its instructions through a few layers of shell scripts.
 root like permissions
root like permissionsI am setting up a few Linux machines for the development group and I don't want them to have root access, but they need to be able to install packages and whatnot. Is there a way to do this? I tried logging them in as root and the 1st thing they did was change root password - so that idea no good. Is there a way to make them a root clone but not able to mess with roots password and other such files? Similar to a Windows Power User?
[David Mandala] What you are looking for is the sudo command. You can let specific users do specific things that (a limited subset) root can do. This can be by person or groups of persons.
man sudo.
[Jason Creighton] Well......this is a tricky question, because if you set up 'sudo' to let them use 'rpm', they'll just write a clever RPM that does Bad Things(tm). So, what you could do is something like this:
- Tell them to install software in their home directories. Compile the software from source, setting the --prefix option to point to somewhere that user can write to. Then have them adjust PATH and whatnot to point to include the right directories.
- Use User Mode Linux. (http://user-mode-linux.sourceforge.net) This would set up a virtual linux machine that they could be "root" in, but wouldn't affect the rest of the machine.
With a particularlty tricksy mind, it's possible to set up a sudo to make people only have access to a command when they are using the right parameters. It could get ugly pretty quick though. I like the user mode linux plan. If you've got some developers working on the same project, you might even lock them into the same virtual machine, and let them share full ownership inside it. You will want to keep an eye on the machines for unusual behavior - defensively and in everyone's best interests, of course. -- Heather
 UPS Problems..
UPS Problems..I recently got an APC SmartUPS700 for my debian server from a friend. I installed it (although without the serial connection, so the server really shouldn't know that it's there) and an hour or two later my server did something strange - it rebooted itself abruptly, on its own accord. I naturally figured this was something to do with the UPS and since it was late at night and i didn't feel like troubleshooting at the time, i took the UPS out of the picture altogether, and rebooted my server, plugged straight into the mains.
Same thing happened.
This has never happened before and I can't figure out why it's happening. At first i thought it must be a hardware problem, perhaps the UPS has somehow damaged the power supply of the server or something like that - but when I booted it into windows and left it for a few hours nothing happened. It only ever happens in linux.
I really don't know what to do to fix the problem, and it's really getting to me - i can't listen to any music, surf the web, do email (i'm rushing to get this written before the computer reboots - the time seems random, anything from 5 minutes uptime to 3 hours..) or anything else..
[Dan Wilder] Very likely hardware. Not likely anything the UPS did.
First thing to do is check memory. I recommend memtest86,
http://www.memtest86.com
If it finds problems, you certainly have a problem. If it doesn't it still doesn't mean all is well with hardware or even memory. Let it run at least four complete passes.
Also make sure your processor cooling fan is working and there's no excessive dust buildup on the processor heat sink or the motherboard chipset heat sink, if any.
[Ben] I'll strongly ditto that one. Wind0ws doesn't "work" the memory as hard as Linux does, particularly if you do something like compiling a kernel. Wind0ws also treats a number of core errors as warnings - viz. the GPFs and the BSODs ("Blue Screen of Death") - whereas Linux will dump core on pretty much any core error. That policy has lead to a kernel that is as bug-free as possible, and the process still goes on.
[Ken Dodge] I agree with Dan. I ran across a similar problem with a Win2K box I had built for my daughter (EPoX EP-8KHA, 1.4GH Athlon) that would continually reset, sometimes even before completing a boot cycle. She, too, couldn't depend on it to get anything done. I eventually found a flakey DIMM, using memtest86. All has been fine since pulling it out (well ... it IS still running Win2K, but that's another problem!)
[Jason Creighton] Yep. I had a problem once with a box crashing that looked like bad memory. Turned out that I had EDO turned on in the BIOS but I didn't had EDO RAM in the box. But in most cases it's bad memory. If you're really hard up for memory, (Just buying more memory would be much easier) you might want to patch your kernel to support "BadRAM". You can tell the kernel to not use certain parts of memory. Here's the URL for that:
http://rick.vanrein.org/linux/badram
memtest86 has an option to output patterns that BadRAM can understand.
[Dan WIlder] Also make sure your processor cooling fan is working and there's no excessive dust buildup on the processor heat sink or the motherboard chipset heat sink, if any.
[Ben Okopnik] Or in the power supply vents. Make sure that your power supply fan is running, too - I've seen that cause more reboots than I could count.
 To find out what's in an RPM
To find out what's in an RPM(see question in mailbag, Gazette 4/2003)
To emulate rpm's query on a .rpm file, just use gnu's less on it. Simple. Nice filter. It shows you the info, patches and files.
Since the source for less is available, it might give him a direction...
Gary Sears
[Jason Creighton] less doesn't do this. Look at the program named in the LESSOPEN enviromental varible. On most distos, it's a script that calls diffent programs depending on the filename. For example, if it's tag.gz or .tgz
tar -tzvvf filename.tgz
to view the contents of a tarball. Or, on my system,
rpm -qpvl filename.rpm
if it's an RPM.
[John Karns] Very cool. I had wondered how less was able to handle gzipped text files. Didn't know it (via $LESSOPEN=lesspipe.sh ... at least on SuSE 7.x) was config'd to handle rpm and some others as well.
 Greetings from Heather Stern
Greetings from Heather SternWe got a decent number of juicy Tips this month. And despite the incredible effort Dan puts into clobbering them, a record number of spams leaking through. Oh well. (Mind you, "record" is something like almost 20. This beats the crap out of the ratios we used to see... Yay for Dan!)
From a "peeves of the month" point of view though (hey, I haven't done those in a while) we also got a record number of people whose mail is quoted-printable in the text portion AND carrying useless HTML around with it. Super ouchie! Rick has long since macro'd his respone to the mime header to tell people how to undo that... I usually have some funnin' on them... such as, "Argh! I need to stomp out all these dratted =2E thingies!" You get the idea.
In the land of Linux itself - Hey, the household firewire pretty much works, USB runs great, we've got sound support coming out of... errr, into our ears... at least around my household, things are looking good. What's eating you that Linux isn't doing for you? Ask the Answer Gang - maybe it's not as hard as all that, or we can point you at who's picking up on that task.
My local Starship and free software group is running an Internet Lounge at the local science fiction convention in my area, Baycon. If you'll be in the San Jose area around the end of the month, drop on by and maybe you can meet a few us who live around here. Or just have a silly time in the 24th century.
Sorry for the short column this time folks. Have a happy.
 Re: Hidden master DNS
Re: Hidden master DNSFrom Dan Wilder
![]() How do you do the hidden master trick for DNS? In my case, my computer
is the real master and my friend runs two secondaries. However, the
registrar lists only his servers. Is that all that's needed to make
his secondary appear to be the master from the public's
perspective, or do I have to do something else too?
How do you do the hidden master trick for DNS? In my case, my computer
is the real master and my friend runs two secondaries. However, the
registrar lists only his servers. Is that all that's needed to make
his secondary appear to be the master from the public's
perspective, or do I have to do something else too?
[Dan] First bear in mind that "master" and "slave", a relationship between servers, has nothing whatever to do with "primary" and "secondary", an arbitrary ordering of servers on a list your registrar maintains for you. Many sysadmins confuse the two, partly because similar terms are sometimes used, and much grief results.
1) List any servers you think will serve your domain with your registrar, in any order you please.
2) Set up any relationship you want between your DNS servers. The master/slave relationship is established (when using BIND) in the named.conf stanzas. For the master:
zone "mydomain.com" {
type master;
file "mydomain.com";
};
and put the "mydomain.com" zone file where the server expects to find it.
For a slave:
zone "mydomain.com" {
type slave;
masters { xxx.xxx.xxx.xxx; };
file "mydomain.com";
};
the slave will download mydomain.com from the master.
About "hidden":
You don't have to list the actual master server at all. It is sufficient that the listed servers know the IP address of the actual master. The registrar doesn't need this information. Then it's a "hidden master".
Somewhat related to this is so-called "split DNS". Use this when you have a firewalled network containing hosts known internally as a part of your domain, but which are not visible outside.
Set up a master DNS server inside and point all your hosts at it. In the "options" section:
options {
...
notify no;
allow-transfer { none; };
forward only;
forwarders {
xxx.xxx.xxx.xxx;
xxx.xxx.xxx.xxx;
xxx.xxx.xxx.xxx;
};
};
which turns off notification to anybody, allows nobody to get a copy of locally maintained zone files, and specifies a few nameservers, typically those of your ISP, as the places to query for domains the server doesn't consider itself definitive for.
Then, for your own domain, a stanza that says:
zone "mydomain.com." IN {
type master;
file "mydomain.com";
};
and the "mydomain.com" zone file contains records for internal hosts, plus all external hosts listed in the mydomain.com zone file in the outside nameserver.
![]() All my domains are "master" in my /etc/bind/bind.conf. My friend has
who-knows-what settings to download my information to his secondary
servers. I'm not sure whether the records appear as "master" or "slave"
on his server. I want his first secondary server (the one listed first
at the registrar) to appear authoritative to the public, so that the
public won't be querying my server. Does he have to do anything else?
I asked him, but he said he thought hidden master was something I set at
my end.
All my domains are "master" in my /etc/bind/bind.conf. My friend has
who-knows-what settings to download my information to his secondary
servers. I'm not sure whether the records appear as "master" or "slave"
on his server. I want his first secondary server (the one listed first
at the registrar) to appear authoritative to the public, so that the
public won't be querying my server. Does he have to do anything else?
I asked him, but he said he thought hidden master was something I set at
my end.
[Dan] Nope.
"Hidden" is set at the registrar. That is, you don't register your server. That makes it hidden.
Your server has to consider itself "master" but that's already set up.
If you want your hidden master to actually control anything, your friend has to set the stanza for your domain in his named.conf file to "slave" with the ip of your machine in the "masters" keyword in the stanza. That's what makes your server a "master".
Or else he has to set his stanza to "master", and you have to send him a copy of your zone file every time you change it, and he has to put it in place. But then your machine isn't a "hidden master".
If the transfer happens on a timely basis, nobody outside cares how the zone file gets to his machine. If he'll cooperate it saves work on your part and on his.
![]() He's already set up to automatically pull the data from my server; that
was set up years ago. I guess that means he's a "slave". But I thought
"secondary" was the term for that, and that his record would tell the
public to go to my server for the authoritative source, but I guess
that's not the case.
He's already set up to automatically pull the data from my server; that
was set up years ago. I guess that means he's a "slave". But I thought
"secondary" was the term for that, and that his record would tell the
public to go to my server for the authoritative source, but I guess
that's not the case.
[Dan] No. That's the confusion due to similar terms being used in the same context for different things, that I've been fighting off and on about with slightly underqualified sysadmins who don't realize the extent of their underqualification, for years.
"Primary" and "Secondary" should be used to denote a matter of public record, the nameservers listed with a registrar for a domain. They should never be used to denote the private relationship between servers, of which the registrar knows nothing.
"Master" and "Slave" should be used to denote a privately arranged relationship between servers configured to furnish DNS information about a particular domain. This has nothing to do with the matter of public record mentioned previously.
 Virtual LINUX
Virtual LINUXFrom Dan Wilder
Answered By Dan Wilder, Rick Moen, Jim Dennis, Heather Stern, Huibert Alblas, Jason Creighton, Jimmy O'Regan, Ben Okopnik
![]()
>Content-Transfer-Encoding: quoted-printable
[Heather] eeek! I hate stomping out all these little extra = and =2E thingies
Unless, of course, you're really defending some foreign letterset from destruction by mail programs. Then it's kinda useful.
Don't do this. Here's how not to: http://expita.com/nomime.html#outlook5
![]() Dear Sir,
Dear Sir,
[Heather] We're "The Answer Gang"
We answer Linux questions, and crossover stuff like this is cool too.
![]() I'm using Windows XP Pro on my home workstation. Which 3rd party
applications would allow loading & "running" Redhat8 from RAM as a
virtual machine? If none which 3rd party applications might emulate
Redhat8? Are any shareware (freeware)?
I'm using Windows XP Pro on my home workstation. Which 3rd party
applications would allow loading & "running" Redhat8 from RAM as a
virtual machine? If none which 3rd party applications might emulate
Redhat8? Are any shareware (freeware)?
[Heather] RedHat 8 fits in RAM? Wow. I want your computer. It must be really expensive. No wonder you can't afford more commercial software for it
I'll translate that as "need to run Linux without ruining my copy of Windows", hope that's ok.
![]() I'm studying network security and need to run or emulate Redhat8 on
XP (preferably without partitioning NTFS for dual boot) to pass the
tests.
I'm studying network security and need to run or emulate Redhat8 on
XP (preferably without partitioning NTFS for dual boot) to pass the
tests.
[Heather] Ok, that clarifies why you want to make sure it's Red Hat that you run. The instructor wants it?
They don't have their own live-CD as far as I can tell, but somebody put some extra effort into basing one off of a Red hat 7.3 distro - perhaps that will be close enough. Or maybe the live flavor isn't handy because RH just released 9, and haven't finished up a demo disk yet. Who knows. Anyways, you can try this one: http://sourceforge.net/projects/emergencycd2
If you really just need a Linux of some sort and your instructor was thinking of RedHat because it's the only distro he knows, perhaps you'd like one of the flavors which can install into your Windows disk space without repartitioning. Look at http://old.lwn.net/Distributions under the heading "DOS/Windows install".
Or, it can be noted that while RedHat really soaks up the disk space on older hardware, is someone has a paperweight computer around, you could boot it off of one of the many floppy based distros easily. Nearly all Linux flavors have similar networking abilities, though only the fancier ones will have cool stuff like samba support.
I hope the extra stuff below is helpful too, and makes your road to network techieness a little more fun.
[Dan] Vmware
But it'd be a lot cheaper, not to mention faster, to purchase a spare hard drive and install Red Hat on it.
[Rick] As Dan Wilder points out, you may have asked the wrong question.
[Heather] While I agree with the guys that it seems like you may be looking for the opposite answer, I'm gonna go out on a limb and answer the question you actually posed. It's probably overkill, but heck, we specialize in that around here
Mostly 'cuz the juiciest bits get pubbed in Linux Gazette for the world to read. So forgive me if I shoot off on a few tangents.
(and for some repeated info, as a few of these products can live in Windows, carrying Linux on their shoulders, or the other way around.)
The company "VMware" makes a reasonably good virtual machine product. I haven't kept track of whether they can run in winXP as the host yet but it seems likely. 'Course they sell their host for Linux, as well, and you would be able to host MSwin or many other OS' under that. It may interfere with MS' nefarious plans for your computer a little, but it's really great for rolling back the damage from any virii that come after you. They do have a trial edition, at least, so I guess that counts as shareware: http://www.vmware.com
...Brief pause while I check whether winXP has joined their extensive list of OS' that can be successfully hosted this way. My own experience shows that win98 can be hosted just fine - but it runs a little slower under this emulation, than the apps themselves do under WINE's direct binary support for MSwin apps. Not that this is perfect mind you, but it's gotten pretty damn good, and there's a handful of commercial vendors helping give WINE a booster shot if you need that. http://www.winehq.com and boatloads of useful links from Rick, below.
- Oh yeah, VMWare's current Workstation product can host all that stuff:
- http://www.vmware.com/products/desktop/ws_features.html
Wow, they've got an SMP edition now too, that is, where the fake PC you get is an SMP box. Scary.
[Halb] It is not free ( costs about $300 ) but a 30 day fully working demo is availble. It emulates a harddisk, networkcard, SVGA card, in short a whole PC. But unlike BOCHS it does not emulate the CPU.
I doubt that you will be able to run VMware with a 2 Gig harddisk completely from ram, but I doubt that you meant running the _complete OS from RAM anayway.
[Heather] 'Course if you were asking this from the point of view of a Macintosh user I'd have to recommend VirtualPC. (warning: Connectix' website isn't clean if you're not running javascript. Dratted bogus redirectors. Grrrrrr.) Doesn't look like they do a Linux edition, but they have it for Windows(tm) too: http://www.connectix.com/products/vpc5w.html
[Jimmy] They have a free trial. I've used it. It's quite nice.
[Heather] At least last time I looked at it 'twas a bit better at hosting Linux than SoftWindows, its competitor, was. Heh, back in our own issue 32 someone asked The Answer Guy if there was a Linux port of it. Well, it looks like Insignia went and sold that off to somebody else, so if someone out there with a PowerMac wants RealPC look for the current vendor: http://www.fwb.com/html/realpc.html
If I believe this news item (http://www.nwfusion.com/newsletters/servers/2003/0303server2.html) then Microsoft is in the process of purchasing either Connectix, or at least its virtual machine stuff. I hope they don't screw up a decent product. It did mention one more commercial competitor though, SW-soft. Their "Virtuozzo" looks like it's on way too grand a scale for what you need to do. I doubt they have much to fear from MS: http://www.sw-soft.com/en/products/virtuozzo
However, you wanted something free as in bucks. Or cheap anyway. I can assure you these vendors have put some effort into the goodies, but let's look at that.
Frankly, TUCOWS is a much better place to look for MSwin shareware than the linux-questions-only folks: http://www.tucows.com
Normally I'd leave you to your own homework there, but I'm curious if anything new has cropped up that would let the MSwin-bound run Linux. Unfortunately surfing their site has become more painful than it used to be; I seem to recall being able to find small product blurbs, on the order of the paragraph or two found at freshmeat for projects listed there. Even one-liners would have been nice. I mourn the demise of more pleasant interfaces like the "program manager" style icon map that winfiles.com used to have before zdnet inhaled them. Hitting up Google for the "windows virtual download" idea finds me an easier to use shareware trove - maybe you'll find it handy. I didn't find more virtual machines there, but I stopped looking after awhile. At least this one's search widget looks in the descriptions as well as titles: http://www.sofotex.com
Linux, of course, is free if you want to spend some time downloading it, or pretty darn cheap if you choose the right place to buy your ISOs and don't need a manual. So perhaps we can look at virtual-machine projects under Linux.
For Linux under Linux, there's User Mode Linux, usually abbreviated to UML. A few of the folk on the lnx-bbc project use it to test the builds. Looking for it via Google! finds me both http://user-mode-linux.sourceforge.net (hey cool! It's available as debian packagesEven better, this page has a lot more content and organization than most SourceForge hosted sites) and http://usermodelinux.org (a PHP-nuke community board, looks like it's got lots of juicy links too). Also, the white paper "Know Your Enemy: Learning with User-Mode Linux" at http://project.honeynet.org/papers/uml might serve as a nice quick Howto for getting it spun up and useful.
See Nick Weber's article this issue for UML. -- Heather
[Heather] Maybe some of the free and opensource projects listed on Freshmeat will work on MSwin environments too? Well, what the heck, can't hurt to look. Both this and a search on TUCOWS for "virtual machine" are likely to hit a few extra links for Java stuff, numerous other OS emulators, and some bytecode-modelled programming environs. Oh well, comes with the buzzword...
Wow. I didn't know there was a liveCD flavor of Linux for hosting UML sessions - the ADIOS project. That's more like it: http://dc.qut.edu.au/adios
While I'm tipping my hat to the Mac folk there's a virtual-machine for running MacOS under Linux/PPC. Basically it seems to be a shim allowing access back to the Mac hardware so you can run another OS ... even more flavors of Linux/PPC, if you like: http://www.maconlinux.org
The analogous project for the PC-compatible platform is currently named Plex86, used to be called FreeMWare. Of course GNU's savannah project is roughly similar to SourceForge, so if a project doesn't wanna make it easy to find their FAQ or other docs, you'll have to thrash around on your own. Anyways it looks like their win32 port isn't terribly useful yet: http://savannah.nongnu.org/projects/plex86
[Jimmy] A patch is available (http://savannah.nongnu.org/patch/?func=detailpatch&patch_id=238&group_id=869) which allows you to use it as an NT host, but AFAICT you'll need Visual C++ to compile it.
[Heather] The folks there recommend "bochs" for emulating a 32-bit PC on non-PC hardware. (I know, they haven't made Windows for non-PC hardware in a coon's age. Oh well.) As far as I know bochs runs on PCs also, so that might very well do the trick. http://bochs.sourceforge.net
It seems likely that it would be much easier to set yourself up with a runs-from-CD setup, if you want it in RAM simply 'cuz you don't want to ruin a local hard disk while experimenting a little. Many Linux vendors offer "live CD" editions of their stuff to whet your whistle. I can't blame you for asking us, since my own quick glance around their website doesn't seem to reveal Red Hat as one of them.
[Rick] ...how to preserve access to the few legacy proprietary Win32 applications...
[Jason] It's interesting you should mention this, I was just thinking about legacy applications for Linux the other day.
[Rick] Once or twice, just to make sure it can be done, I dig out a source tarball from the vanished world of 1992 Linux, and see if it can be still made to compile and run. The answer is usually "You bet". 11 years of compatibility is pretty good, esecially given that the OS was brand-new back then.
[Ben] Interesting; seems we have a habit in common. I do that myself, occasionally.
I've managed to compile - with either no or minimum tweaking - stuff that K&R wrote way back (found it on the web page where one of them is reminiscing about the Good Old Days.) It's been a few years, but I still remember being pleasantly shocked.
[Jimmy] Maybe you two would be interested in this: http://www.southern-storm.com.au/v7upgrade.html
- a project to make Unix V7 work on Linux
[Rick] Hey, cool! I'll have to install it, fire up teco, and UUCP you some mail about it.
[Ben] Pardon me, I'll just go to the corner and retch quietly...
(Great Ghu, what a sick idea. Worse yet, there's a "teco.el" for Emacs... talk about coming full circle.)
[Heather] I'm afraid I have to take full blame for that one. I asked RMS if the original macros worked under the teco emulator for emacs. He was suddenly just like a little kid -- he just had to know where he could get it, was it free, would they enjoy joining the gnu project, would...
I had to slow him down enough to say that I'd heard of it so I just wondered. I figured he probably had the originals around for old times' sake. He later made sure it got into the standard emacs distro somehow. And yes, he said... they do.
Now that is full circle. Or maybe full toroid. Hmm, donuts...
[Heather] Well, only almost full blame. I didn't write it, I just enabled it to delight/torture/confuse an unsuspecting modern emacs audience.
[Jimmy] I found the sources of the original teco (along with the sources of ITS - Great Gnu indeed!) somewhere, but misplaced the link.
[Rick] Just remember the magic word: "Retrocomputing"! http://www.pdc.kth.se/~jas/retro/retromuseum.html
I personally think that making a teco with ANSI terminal support is cheating, robbing you of that cutting-edge ASR33 experience. (I suppose it would be arch to exclaim "curses!" at this point.)
Kids, these days! Spoiled rotten with their fancy gnome-teco contraptions, I say. The terminal that's not terminal makes you stronger.
[Jimmy] The sources of IBMs OS/360 are out there too - AFAICT in the public domain, because they were published without a copyright notice before some law came into effect.
[Rick] USA copyright law was amended in 1978, to comply with treaty, removing the prior requirement of copyright notices. Until that point, it was possible to lose copyright through omitting notice. _Starting 1978, covered works became subject to automatic copyrigh -- under proprietary terms by default.
Typically, binary-only applications have almost the same longevity of backwards compatibility, if you take care to furnish old support libs (http://linuxmafia.com/wpfaq/downloadwp8.html#FIX, and both source and binary interfaces have if anything standardised.
And this (along with adherence to public standards and documented interfaces) is why we tell people that Linux can help them escape the forced-upgrade treadmill.
[Jason] If/When the next big open source OS comes along (Supposing it isn't a UNIX. If it was, we'd just recompile everything.), we really don't have to worry about supporting our old Linux apps on it as long as it has a terminal emulator and an X11 implementation. Then you could just set up a Linux PC specifically to run programs for other computers on the network.
[Jimmy] You probably wouldn't even need that - Next Big Thing OS would probably have a Unix compatibility layer a la Cygwin written for it. There's already a linux emulator for Cygwin (LINE - http://line.sourceforge.net) and for SysV (LxRun - http://www.ugcs.caltech.edu/~steven/lxrun) as well as the in-kernel stuff that the BSDs have. And you can assume that Bochs and VNC will be ported to this OS.
[JimD] It's possible that the next major non-UNIX OS to take a look at would be EROS. It has a vitally different security model from that of UNIX - a true capabilities system, of which the "privs" in the latest linux kernels are a mere shot in the right direction, and where virtual spaces are part of the basic environment. (http://www.eros-os.org)
[Jason] I'm hoping, that as Microsoft's market share slips, they'll actually have to make their OS compatible with other OSes. Windows 2000 uses Kerberos for network security. Of course, they had to add their own extensions to it, but still, when Microsoft is using a standard protocol, you know something is up.
[Rick] I'm actually more used to answering the reverse question of yours, that of how to preserve access to the few legacy proprietary Win32 applications one might still need after upgrading to Linux.
Accordingly, my stock answer to _that question follows, and you may be able to use some of its suggestions despite your through-the-looking-glass perspective on the problem. E.g., you could use the Win32 version of VMware, running RH9 within its virtual session.
The text below is cited from my WordPerfect on Linux FAQ (http://linuxmafia.com/wpfaq/future.html#ALTERNATIVESWIN32):
8.6. What alternatives to WP exist involving Win32 apps on Linux?
Such alternatives are outside the scope of this document, but include
- the numerous ways of running Win32 applications on Linux in some
%-% -) VMware, Inc.'s VMware, http://www.vmware.com (simulation in a virtual environment of a particular theoretical x86 box's hardware, which then can boot various OSes including Win9x/ME/NT/2k/XP within the emulated environment, necessitating a copy of that OS, as well),
-) NeTraverse's Win4Lin, http://www.netraverse.com (an MS-Windows 9x/ME emulation environment for x86 Linux, requiring a copy of MS-Windows 9x/ME to work)
-) WINE, http://www.winehq.com (an LGPLed library and program loader implementing on x86 Unixes the Win32 and Win16 application interfaces)
-) ReWind, http://rewind.sourceforge.net (an MIT/X11-licensed fork of an earlier WINE release),
-) CodeWeavers's Crossover Office, http://www.codeweavers.com/products/office (WINE with some extra support for MS Office applications)
-) CodeWeavers's Wine Preview, http://www.codeweavers.com/technology/wine (an MIT/X11-licensed variant of an earlier WINE release tweaked for stability, and with an improved installer)
-) CodeWeavers's Crossover Plugin, http://www.codeweavers.com/products/crossover (WINE variant for x86 Linux to support Web browser plugins such as QuickTime)
-) TransGaming Technologies, Inc.'s WineX, http://www.transgaming.com (another WINE extension for x86 Linux, with enhanced DirectX support, primarily for 3D games)
-) the Bochs Project's Bochs, http://bochs.sourceforge.net (software environment for any CPU family emulating an entire x86 CPU, common I/O devices, and BIOS),
-) and Drew Northup's Plex86, http://savannah.nongnu.org/projects/plex86 (software environment emulating on x86 a virtual x86 session),... %-%
...and
- the numerous ways of remotely running Win32 applications from
- RealVNC Limited's VNC Server, http://www.realvnc.com
- Constantin Kaplinsky's TightVNC, http://www.tightvnc.com
- Tridia Corporation's TridiaVNC, http://www.tridiavnc.com
- and Matt Chapman's rdesktop, http://www.rdesktop.org
I maintain a listing (http://linuxmafia.com/~rick/linux-info/vnc-and-alternatives) of options in the latter category.
![]() Thank you all for your answers to my question. I actually do
appreciate the time most of you took to give me alot of information. To
answer some of your questions: Yes I do have an expensive machine. I've
an 80GB HDD partitioned NTFS so, although I have the space, I'm not
going to repartition to install LINUX nor buy another HDD. I've 512MB of
RDRAM with 566MHZ FSB & a 2.27GHz P4. (Yes, I'm a hardware geek). I can
understand your pro LINUX position but frankly, hardening the security
of a server from the command line is difficult, but you can't beat free,
now can you?
Thank you all for your answers to my question. I actually do
appreciate the time most of you took to give me alot of information. To
answer some of your questions: Yes I do have an expensive machine. I've
an 80GB HDD partitioned NTFS so, although I have the space, I'm not
going to repartition to install LINUX nor buy another HDD. I've 512MB of
RDRAM with 566MHZ FSB & a 2.27GHz P4. (Yes, I'm a hardware geek). I can
understand your pro LINUX position but frankly, hardening the security
of a server from the command line is difficult, but you can't beat free,
now can you?
Anyway heartfelt thanks for your time and effort.
Imrahil O'Belalas
|
...making Linux just a little more fun! |
By Michael Conry |
|
Contents: |
Submitters, send your News Bytes items in PLAIN TEXT format. Other formats may be rejected without reading. You have been warned! A one- or two-paragraph summary plus URL gets you a better announcement than an entire press release. Submit items to gazette@ssc.com
 May 2003 Linux Journal
May 2003 Linux Journal
![[issue 109 cover image]](misc/bytes/lj-cover109.png) The May issue of Linux
Journal is on newsstands now.
This issue focuses on Kernel Internals. Click
here
to view the table of contents, or
here
to subscribe.
The May issue of Linux
Journal is on newsstands now.
This issue focuses on Kernel Internals. Click
here
to view the table of contents, or
here
to subscribe.
All articles older than three months are available for
public reading at
http://www.linuxjournal.com/magazine.php.
Recent articles are available on-line for subscribers only at
http://interactive.linuxjournal.com/.
Some tips from Linux Journal on experimenting with the 2.5 kernel.
Linux Journal report on LinuxWorld Ireland 2003.
Building a Linux Media Jukebox to handle digital photos, audio, video, DVD and TV.
Massachusetts-based Open-Pc founder/CEO Morgan Lim discusses the business he has built around Linux.
Fujitsu preps Linux-based robot. It is based on a real-time Linux running on a 700MHz Pentium III.
Some links highlighted by Linux Today:
Managing Linux releases for large numbers of installations.
Keith Parkansky's linux tips website www.aboutdebian.com has a series of "hands on" walk-throughs to help Linux beginners go from the basics to server and firewall setups while doing some fun things (like killing a telnet process to cut someone off) along the way. The material is particularly relevant to Debian users, but mostly it will be useful to anybody using GNU/Linux.
Richard Stallman on why he refused to speak at the eGovOS conference.
Using Free (Open Source) Software in a Grassroots Organisation. Reports on the use of Linux at the Low-Income Networking and Communicaitons Project of the Welfare Law Center.
Listings courtesy Linux Journal. See LJ's Events page for the latest goings-on.
|
Penguicon | May 2-4, 2003 Warren, MI http://penguicon.sourceforge.net/ |
|
USENIX First International Conference on Mobile Systems,
Applications, and Services (MobiSys) | May 5-8, 2003 San Francisco, CA http://www.usenix.org/events/ |
|
Linux Clusters Workshop in France | May 12-16, 2003 IBM Montpellier Laboratory http://www.linuxclustersinstitute.org |
|
Third Open Source Content Management Conference | May 28-30, 2003 Cambridge, MA http://www.oscom.org |
|
CeBIT America | June 18-20, 2003 New York, NY http://www.cebit-america.com/ |
|
ClusterWorld Conference and Expo | June 24-26, 2003 San Jose, CA http://www.clusterworldexpo.com |
|
O'Reilly Open Source Convention | July 7-11, 2003 Portland, OR http://conferences.oreilly.com/ |
|
12th USENIX Security Symposium | August 4-8, 2003 Washington, DC http://www.usenix.org/events/ |
|
HP World | August 11-15, 2003 Atlanta, GA http://www.hpworld.com |
|
LinuxWorld UK | September 3-4, 2003 Birmingham, United Kingdom http://www.linuxworld2003.co.uk |
|
Linux Lunacy Brought to you by Linux Journal and Geek Cruises! | September 13-20, 2003 Alaska's Inside Passage http://www.geekcruises.com/home/ll3_home.html |
|
Software Development Conference & Expo | September 15-19, 2003 Boston, MA http://www.sdexpo.com |
|
PC Expo | September 16-18, 2003 New York, NY http://www.techxny.com/pcexpo_techxny.cfm |
|
COMDEX Canada | September 16-18, 2003 Toronto, Ontario http://www.comdex.com/canada/ |
|
IDUG 2003 - Europe | October 7-10, 2003 Nice, France http://www.idug.org |
|
LISA (17th USENIX Systems Administration Conference) | October 26-30, 2003 San Diego, CA http://www.usenix.org/events/lisa03/ |
|
HiverCon 2003 | November 6-7, 2003 Dublin, Ireland http://www.hivercon.com/ |
|
COMDEX Fall | November 17-21, 2003 Las Vegas, NV http://www.comdex.com/fall2003/ |
 Linux Test Project
Linux Test Project
 Eventide
Eventide
Eventide Inc., a producer of digital logging technology, have created a Linux-based digital logging and archiving system capitalising on the stability and reliablility of GNU/Linux. Such reliability is crucial in the public safety marketplace during mission critical situations.
The specifications of the Eventide VR778 digital logging and archiving system are available in pdf format. Eventide claims that the VR778 is the first digital logger to use the Linux O/S. This enables Eventide to provide a highly sophisticated digital system with no licensing requirements and an O/S that does not carry any other applications overhead "like many other Microsoft server based systems".
 Anti-Spam Task Force Established by ActiveState
Anti-Spam Task Force Established by ActiveState
ActiveState Corp., a producer of email content filtering software, has announced the creation of an internal blue ribbon team comprised of the world's foremost anti-spam researchers. The Task Force members include: Dr. John Graham Cumming, creator of the popular open source Perl-based Bayesian mail filtering program, POPfile; Tim Peters, creator of SpamBayes, a Python-based open source Bayesian email classifier; Jason Rennie of MIT's Artificial Intelligence lab and creator of the open source tool, ifile, an automated email classification system; and Gary Robinson, an innovator in collaborative filtering. The Task Force is focusing on anti-spam issues affecting the enterprise, and is led by ActiveState's Director of Development, Jesse Dougherty.
The Anti-spam Task Force is focusing on several technical initiatives to optimize enterprise email messaging, including:
 Ark
Ark
Ark Linux H20: Simple and (Nearly) Complete.
 Knoppix
Knoppix
Knoppix 3.2 has been released
 Linux From Scratch
Linux From Scratch
The latest version of LFS (4.1) will be available in printed-book form. The book will be available with or without companion CDRom from CheapBytes.
When you have your LFS 4.1 system up and running, you can get stuck into BLFS (Beyond LFS) which has just been updated to version 1.0.
 Lindows
Lindows
 Mandrake
Mandrake
Mandrake Linux releases 9.1.. This relese has been reviewed at OSNews (links courtesy Linux Today).
 PCQLinux
PCQLinux
NewsForge reports on PCQLinux. An Indian monthly magazine, PCQuest, has released its own variant Linux distribution based on Red Hat Linux 8.0.
 Peanut
Peanut
 Slackware
Slackware
Slackware 9.0 has been released. Check out the ChangeLog to see what's new.
This release has been reviewed at TinyMinds.org, while OSNews debunks some myths surrounding the distribution (courtesy Linux Today).
 UnitedLinux
UnitedLinux
UnitedLinux has announced that its four founding partner companies will offer special support programs and discounts to ISV participants in the Oracle's Unbreakable Linux Partner Initiative.
 Yellow Dog
Yellow Dog
 Phoenix Rises From Ashes As Firbird
Phoenix Rises From Ashes As Firbird
The name of the Mozilla spinoff browser Phoenix has been changed to Firebird.
 Kerio Adds SpamAssassin to Latest Mail Server Release
Kerio Adds SpamAssassin to Latest Mail Server Release
Kerio Technologies, a security solutions software developer has launched the new version of its multi-platform corporate messaging solution, Kerio MailServer 5.6 with augmented anti-spam protection. Existing anti-spam tools have been enriched by the award-winning spam detection technology: SpamAssassin.
Kerio has also formed a partnership with Sophos to fight viruses in emails.
 CourseForum/ProjectForum 2.1
CourseForum/ProjectForum 2.1
CourseForum Technologies has announced the availability of both CourseForum 2.1 and ProjectForum 2.1. These web-based applications are intended to bring enhanced interaction, coordination and communication to online or face-to-face courses, student groups, workgroup projects, business teams, and corporate intranets. CourseForum and ProjectForum can be hosted on Mac OS X, Windows, Linux and FreeBSD. Users need only a standard web browser.
 iConductor Goes Shareware
iConductor Goes Shareware
The iConductor Server Module designed to simplify the development of rules-based web applications on the Apache server is now available as shareware, including for the Apache Version 2.0. iConductor's creator, Farpointer Technologies, has changed its distribution model to allow unrestricted distribution of the iConductor module for non-commercial purposes. The target market is Linux-based Apache server users.
 Other software
Other software
Mick is LG's News Bytes Editor.
![[Picture]](../gx/2002/tagbio/conry.jpg) Born some time ago in Ireland, Michael is currently working on
a PhD thesis in the Department of Mechanical Engineering, University
College Dublin. The topic of this work is the use of Lamb waves in
nondestructive testing. GNU/Linux has been very useful in this work, and
Michael has a strong interest in applying free software solutions to
other problems in engineering. When his thesis is completed, Michael
plans to take a long walk.
Born some time ago in Ireland, Michael is currently working on
a PhD thesis in the Department of Mechanical Engineering, University
College Dublin. The topic of this work is the use of Lamb waves in
nondestructive testing. GNU/Linux has been very useful in this work, and
Michael has a strong interest in applying free software solutions to
other problems in engineering. When his thesis is completed, Michael
plans to take a long walk.
|
...making Linux just a little more fun! |
By Shane Collinge |
These cartoons are scaled down to minimize horizontal scrolling. To see a panel in all its clarity, click on it.
All HelpDex cartoons are at Shane's web site, www.shanecollinge.com.
![[BIO]](../gx/2002/note.png) Part computer programmer, part cartoonist, part Mars Bar. At night, he runs
around in a pair of colorful tights fighting criminals. During the day... well,
he just runs around. He eats when he's hungry and sleeps when he's sleepy.
Part computer programmer, part cartoonist, part Mars Bar. At night, he runs
around in a pair of colorful tights fighting criminals. During the day... well,
he just runs around. He eats when he's hungry and sleeps when he's sleepy.
|
...making Linux just a little more fun! |
By Javier Malonda |
The Ecol comic strip is written for escomposlinux.org (ECOL), the web site that supports, es.comp.os.linux, the Spanish USENET newsgroup for Linux. The strips are drawn in Spanish and then translated to English by the author. Text commentary on this page is by LG Editor Iron. Your browser has shrunk the images to conform to the horizontal size limit for LG articles. For better picture quality, click on each cartoon to see it full size.
These cartoons are copyright Javier Malonda. They may be copied, linked or distributed by any means. However, you may not distribute modifications. If you link to a cartoon, please notify Javier, who would appreciate hearing from you.
|
...making Linux just a little more fun! |
By Bruce Forsberg |
Recently I have been looking for an MP3 player that would satisfy several criteria. One, be usable with Linux and second, be usable with Old Time Radio shows. I am a big fan of what is called Old Time Radio here in the USA. This is radio shows from the 1930's, 40's, and 50's. One can buy a CD-R full of shows all in MP3 format. OTR shows are typically encoded at 24, 32, or 48 kbps in mono format with a sample rate of 22050 and are 1/2 hour to 1 hour in length. Not all MP3 players work well under these conditions. Thus began my search for a better solution. After some search I came to the conclusion that a Linux PDA would be my best bet where I could write custom software to perform the needed functionality that is required. Since the Sharp Zaurus SL-5500 uses Linux with Qtopia, a Qt system for embedded systems, this became an obvious choice since I already know Qt programming on Linux.
When I looked at the Sharp web site I saw two Linux PDA models present for sale in the USA. The SL-5500 and the SL-5600. At the time of writing this article the SL-5600 has just become available. There are several main differences between the two models but the main one is that the SL-5600 contains a 400 Mhz Intel Xscale processor whereas the SL-5500 contains a 206 Mhz Strong ARM SA-1110 processor. I decided on the SL-5500 since that was the only option when I bought. The 400 Mhz would be nice but not needed for audio. If I wanted video I would have waited for the 5600. This device contains a Linux 2.4 Embedix kernel stored in a 16 MB Flash ROM with many other standard applications. It contains 64 MB SDRAM of which about half is used for program memory usage and the other half for user program storage. It contains a host of accessories and other capabilities.
I was able to purchase my Sharp Zaurus SL-5500 new on EBAY for about $300 plus $20 shipping. It came with a docking station with a USB connector and software for MS Windows. That was several months ago. Now that the SL-5600 has come out the SL-5500 is selling for about $200-$300 new.
In order to learn how to program on this platform I decided that my OTR MP3 project was too big for a first project so I choose a simpler project. It is a car mileage calculator. I just purchased a Toyota Prius Hybrid automobile. Since I get around 45-50 MPG I like to track my mileage. So I wrote down a few requirements for the program and started out on how to program for the SL-5500 PDA. The following are my findings.
First you will need several pieces of software. When you develop for the Sharp Zaurus you will develop in two phases. You will perform all your GUI layout, coding, debugging, and testing on your Linux Intel box. Then when you have finished that, you will cross-compile and package the software for the Sharp Zaurus PDA using the Strong ARM architecture. You will need several RPMs to accomplish this. Here are the packages that you will need.
qtopia-free-1.X.X-1.i386.rpm -- Qtopia SDK for Linux Intel. Get the latest from Trolltech's web site.
binutils-cross-arm-2.11.2-0.i386.rpm -- Arm binary utilities for Linux Intel
gcc-cross-sa1100-2.95.2-0.i386.rpm -- Arm cross compiler for Linux Intel
glibc-arm-2.2.2-0.i386.rpm -- Arm glibc
linux-headers-arm-sa1100-2.4.6-3.i386.rpm -- Arm header files
The above 4 files can be obtained from the Zaurus Documentation web site along with instructions on how to install them.
To begin with you will need the standard stuff that comes with your Linux on Intel distribution for compiling C++ programs. Next you will need to install the Qtopia SDK (Software Development Kit). Please note that there is a commercial SDK as well as a free SDK. If you use the free SDK you might be limited as to the licensing of your program. Be sure to read Trolltech's information regarding this. Once this is installed you will be able to compile, run, and debug on your Linux on Intel box. When this is done and you are ready to test your program you will need to install the last 4 rpms listed above. This will give you the ability to cross compile your program for the Strong ARM processor.
Now that you have development setup you are ready to start developing. If you have never developed before, the Sharp Zaurus is the ideal platform. This is because of limited storage and memory the best programs are simple programs. Full function office suites are not wanted. If you need an idea then I suggest you look at program search engines for the Palm and Microsoft OS PDAs. Then look at the Zaurus PDA search engines. When you find an application that is not available for the Zaurus but is for the others then chances are this is a good choice. Also choose a program that interests you.
Before you get started you will need to set environment variables for developing on your Linux on Intel box. You will need to set the following in your bash shell assuming that you placed the software package in the default location:
QPEDIR=/opt/Qtopia
QTDIR=/opt/Qtopia
TMAKEPATH=/opt/Qtopia/tmake/lib/qws/linux-x86-g++/
PATH=$QTDIR/bin:$QPEDIR/bin:${PATH}:/opt/Embedix/tools/bin
LD_LIBRARY_PATH=$QTDIR/lib:${LD_LIBRARY_PATH}
export QPEDIR QTDIR PATH TMAKEPATH LD_LIBRARY_PATH
The next few steps entail developing just like you develop a normal Qt application. I will not go into this since there have been many articles on this already. A good book on the subject is published by O'Reilly and is called "Programming with Qt" by Matthias Kalle Dalheimer. Briefly you will use designer to create your GUIs. Keep in mind that the display is 240x320. Then generate a ui file. Next you will create a project file. Usually called your project name dot pro (ie example.pro). If you need a little help look in the SDK directory /opt/Qtopia/example. This is an example program that contains most of the components needed to build a program. Use this .pro file as a starting point. Once your .pro file is created then you will generate your Makefile by:
tmake -o Makefile yourprogram.pro
Now start your coding. Create your classes and your slots and connections as with ordinary Qt programming. When this is completed then build your program by typing "make". Fix any errors and when you have a successful build then you are ready to run your program in the emulator. Since the Sharp Zaurus has no X server you need an emulator to simulate the environment of the Sharp Zaurus. First you need to run the Qt/Embedded Virtual X11 Framebuffer. In the same shell type:
qvfb &
You should now have an X11 application running that is the emulator. Now you will need to run the equivalent of a window manager. To do this type in the same shell:
qpe &
If everything has gone well then you should see an emulation of a Sharp Zaurus PDA. It is in this environment that you will be able to test and debug your program. Even though you don't see your program all you need to do to have it run is to start it from your development directory. Just run your program normally. You should be able to run it in a debugger as well. You can now fully test your application.
Your next step is to generate an ipkg file that can be loaded onto your PDA and installed. ipkg format is the format used on the Sharp Zaurus PDA. To do this you need to first compile your program for the Strong ARM processor using the cross compiler and tools that you installed in the section above. To start with it is best to start a new shell. Once in this shell setup the following environment variables:
CROSSCOMPILE=/opt/Embedix/tools
QPEDIR=/opt/Qtopia/sharp
QTDIR=/opt/Qtopia/sharp
PATH=$QTDIR/bin:$QPEDIR/bin:$CROSSCOMPILE/bin:${PATH}
TMAKEPATH=/opt/Qtopia/tmake/lib/qws/linux-sharp-g++/
LD_LIBRARY_PATH=$QTDIR/lib:${LD_LIBRARY_PATH}
export QPEDIR QTDIR PATH LD_LIBRARY_PATH TMAKEPATH
Next you need to generate a new Makefile that is for the Strong ARM processor. So type:
tmake -o Makefile yourprogram.pro
Then "make clean" to remove all the old object files. Then "make", you should now be building everything with the cross compiler. Since there is a limit to the size that a PDA can hold I recommend that you strip your executable. But, don't make the mistake that I made and use strip. You need to use the cross compiled strip, in this case arm-linux-strip.
Now that you have your executable you need to package everything in an ipk file. First you need to create a top level directory, we will use prog for our example. Next you need to create the following directory trees:
prog/opt/QtPalmtop/bin prog/opt/QtPalmtop/lib (if needed) prog/opt/QtPalmtop/apps/Applications prog/opt/QtPalmtop/help/en/html prog/opt/QtPalmtop/pics prog/CONTROL
First of all put your executable in the bin directory. If you have libraries as well then put them into the lib directory. Your help file will be in html format. So create a html file with your favorite editor and place this into the html directory. The file name should be your executable name dot html. The directory shown above assumes an english html file (ie en). If you use a different language then you will need to use a directory other than en. In the pics directory place an image file in png format that is 32 X 32 pixels. This will show up as the icon used for this application. This leaves us with two directories, CONTROL and Applications. In CONTROL you will place a file called control. This will be used for ipk. In Applications create a file called yourprogramname.desktop.
For my mileage program I use a control file with the following entries:
Package: mileage Priority: optional Section: Misc Version: 2.0 Architecture: arm Maintainer: Bruce Forsberg forsberg@tns.net Description: A Car Mileage Calculator Program
The Package field contains the name of the package. Priority should be optional for most other applications. Section can be Misc for now but should be changed later to an appropriate value. See the IPKG docs for more information. Version should be the version of your application. Architecture should be arm for the SL-5000 and SL-5500 Zaurus PDAs. Maintainer should be the name and email address of the person maintaining this package. Description should be a brief description of the program. Depends is an optional field if your application depends on other packages being present. See the resources section of this article for more detailed information on the IPKG format.
If you want your icon to show up in the Qtopia desktop you will need to add a desktop file in the Applications directory. For the desktop file for my mileage program I use the entries shown below. The fields should be self explanatory.
[Desktop Entry] Comment=A Car Mileage Calculator Program Exec=mileage Icon=mileage Type=Application Name=Mileage Calculator
Now that we have all these files created and stored into the subtree of prog we are ready to build the package. Use this script and then type "ipkg-build.sh prog". You now have a .ipk file. Simply use the normal methods of loading software onto zaurus and install your program and test it. If you launch your program and nothing happens, one thing to try is to install the qpe-terminal application. This will give you the equivalent of an xterm on the Zaurus. Start the terminal application and enter your application name from this window and see if you get any error messages. Also you can type dmesg. This will display the messages sent to the error log.
I hope this article will inspire you to start programming for the Sharp Zaurus PDAs. It is a lot of fun and adds to the success of Open Source and Linux. You also will be surprised just how much you will wind up using your new PDA. After you finish your project and are ready to release it check out sourceforge.net. This is a great place to host your project. Then upload your ipk to the Zaurus PDA search engine at http://www.killefiz.de/zaurus. Be prepared to release another version in a couple of weeks after the first release. You should fix any major bugs found with this release so that your program will be useable. Also think like a user when you create your program. Make it as easy to use as possible. For example for my mileage program I added a GUI keypad to enter odometer and fuel and a button to enter today's date. Even though the Zaurus has a keyboard, the GUI keypad makes entry so much easier. So, get your Zaurus start developing and have fun.
How to docs for the Sharp Zaurus - http://docs.zaurus.com IPKG How to for Sharp Zaurus - http://docs.zaurus.com/ipkg_howto.shtml IPKG Home Page - http://www.handhelds.org/z/wiki/iPKG IPKG build script - http://docs.zaurus.com/downloads/ipkg-build.sh Programming with Qt book - http://www.oreilly.com/catalog/prowqt2 Sharp SL-5500 - http://www.sharpusa.com/products/ModelLanding/0,1058,698,00.html Sharp SL-5600 - http://www.sharpusa.com/products/ModelLanding/0,1058,1016,00.html Zaurus Developer site - http://www.zaurus.com/dev Zaurus Program Search Engine - http://www.killefiz.de/zaurus Must-Have Zaurus Hardware and Software - Linux Journal Jan 2003 Article, not available on-line yet. Linuxdevices.com article - http://www.linuxdevices.com/articles/AT6553340334.html Car Mileage PDA Calculator Home Page - http://mileage.sourceforge.net
![[BIO]](../gx/2002/note.png) Bruce is just an average guy having fun with Linux. He is the
founder of the
Open Source Audio Library Project.
He got his start programing freeware on
windows 3.1. When he realized that all one had to do was to not
return from a message and it would hang the entire operating
system, he knew there had to be a better way. Linux was the answer.
Bruce is just an average guy having fun with Linux. He is the
founder of the
Open Source Audio Library Project.
He got his start programing freeware on
windows 3.1. When he realized that all one had to do was to not
return from a message and it would hang the entire operating
system, he knew there had to be a better way. Linux was the answer.
|
...making Linux just a little more fun! |
By Ben Okopnik |
- "It's just a little further along... right through here, Frink."
Woomert and Frink had had a long walk along the tunneled VPN connection, their footsteps echoing against the titanium walls; once they reached the comfortable spacious environment of their destination system, Frink had wanted to pull up a comfortable variable and rest his tired feet, but Woomert had insisted on pushing on. Now, Woomert turned and entered the room marked "/var/log/apache"."Ah, here we are - there's `/var/log/apache/access.log' - and just in time from the looks of it. The poor thing is up to 400MB and it's nearly filling up the partition, and it's only been a few days since it was rolled over!"
Frink, having dropped onto the sparkling clean floor (the system had recently been swept by "cruft") and arranging himself in a tailor's seat, stared at the bulging log file in fascination.- "What happened here, Woomert? I just came in to tell you about the latest story in the newspapers, praising you to the sky for your solution to the Missing Databases Mystery [1] at the Bigrich Bank, and you dragged me off without a word. Not that I mind, but..."
The famous detective smiled self-deprecatingly.- "I do tend to get a bit concentrated while on the job, don't I? Oh well - there are worse things. All right, here is what's happening: the client, a small company that specializes in making horseshoe welding sprockets for accountants working in the napkin-fringing industry, has become suspicious of a few odd things happening with their web site. For example, their response time often spikes right through the roof, and they've been returning the `Server busy' message much too often as compared to normal operation. There hasn't been any huge jump in the amount of business they do - less, since the economy these days doesn't permit too many luxuries like their product - so..."
Frink nodded.- "It sounds like a DoS (Denial of Service) attack, Woomert."
- "Indeed." Woomert, deep in thought, pulled on his typing gloves and approached the local terminal. "This is a highly competitive industry, you know. This company maintains its lead by ferret-polishing the final product, but it's a narrow margin; the competitors would all love to get an advantage, and DoSing their web site just might do it. We've been hired to look around and report anything unusual, so this is just a statistics gathering mission.Here, let's test a few things. First, though, lets make a couple of copies of this file where it won't cram things quite as badly... There, I've put them both in `/home/woomert'. We don't really want to lose any of the data if we should accidentally damage or destroy one file, do we? Now, let's zero out the actual log and restart the server... excellent. Now - on to exploring the files. Given that you suspect a DoS - I do, as well - what would you look for, Frink?"
Frink scratched his head and frowned in concentration.- "I'm not sure, Woomert. I think I'd like to figure out the average hits per IP, and then maybe look at the sorted list of the same. That would tell us if someone is really slamming this server and from where, don't you think?"
Woomert smiled happily.- "Why, Frink, that sounds like an excellent idea! Yes, let's take a look at the average:
perl -wlne'/^(\S+)/;$h{$1}++}{print"$h{$_}\t$_"for sort{$h{$a}<=>$h{$b}}keys%h' access.log
12.30830039525692
- "Hmm, interesting. Taking into account that the number is going to be higher due to the very large DoS entries - we're still assuming those, but it's a fair bet - that's not an unreasonable number. Most people will probably examine a few models before making their decision to buy; after all, it is a once-in-a-lifetime purchase. In fact, this company led the rest of the pack in offering lifetime warranties... All right - now let's look at that sorted list:
perl -wlne'/^(\S+)/;$h{$1}++}{print"$h{$}\t$"for sort{$h{$a}<=>$h{$b}}keys%h' access.log
...- "Well, well; would you look at that! What's your estimate, Frink?"
22 users.osceola.k12.fl.us
26 152.31.2.221
26 modem-140.nyc-tc01a.fcc.net
28 62.84.228.7
31 209.106.1.124
103 bdsl.66.13.44.110.gte.net
112 24-164-141-122.si.rr.com
611 nyny01hsiapat.everestbroadband.com
1085 162.66.50.6
2817 web-05.segfl.ifl.net
55055 wsip66-210-242-2.ph.ph.cox.net
71031 205.213.111.53
85120 pc-80-193-117-84-cw.blueyonder.co.uk
97000 151.138.254.21
111092 168.11.225.251
122101 syr-24-92-242-3.twcny.rr.com
155017 212.85.1.1
175990 pool-68-161-90-99.ny325.east.verizon.net
181222 1cust185.tnt15.nyc9.da.uu.net
315078 pool-141-155-115-168.ny5030.east.verizon.net
Frink stared at the screen for a moment, then nodded. When he spoke, there was a confident note in his voice.
- "It's a DoS. I'm willing to believe that someone would spend a day or so browsing this site, so the 103 and the 112 are border cases, but - 315 thousand hits? I don't know that I'd call it a DDoS (a distributed DoS, where many machines at ones are attempting to flood a given network or host) because the number of machines is fairly small, but it should definitely be an issue for further investigation - perhaps contacting the ISPs for those domains - and a temporary block at the firewall. Woomert, could we look at a sample entry for the different hits? I have a theory about this. If it's a long `GET' string, then... I wonder."Woomert looked thoughtful, then nodded.
- "I see where you're going, Frink, and it's a reasonable possibility. Here, this will show the longest entry for a given IP:
perl -lne'/^(\S+).*?"(.*?)"/;length$h{$1}>length$2or$h{$1}=$2}{print"@a"while@a=each%h' access.log
...
pool-68-161-90-99.ny325.east.verizon.net GET /default.ida?XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX%u9090%u6858%ucbd3%u7801%u9090%u6858%ucbd3%u7801%u9090%u685
8%ucbd3%u7801%u9090%u9090%u8190%u00c3%u0003%u8b00%u531b%u53ff%u0078%u0000%u00=a
HTTP/1.0
syr-24-92-242-3.twcny.rr.com GET /default.ida?XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX%u9090%u6858%ucbd3%u7801%u9090%u6858%ucbd3%u7801%u9090%u6858%
ucbd3%u7801%u9090%u9090%u8190%u00c3%u0003%u8b00%u531b%u53ff%u0078%u0000%u00=a
HTTP/1.0
1cust185.tnt15.nyc9.da.uu.net GET /default.ida?XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX%u9090%u6858%ucbd3%u7801%u9090%u6858%ucbd3%u7801%u9090%u6
858%ucbd3%u7801%u9090%u9090%u8190%u00c3%u0003%u8b00%u531b%u53ff%u0078%u0000%u00=a
HTTP/1.0
212.85.1.1 GET /default.ida?XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
XXXXXXXXXXXXXXXXXXXXXXXXXXXXXX%u9090%u6858%ucbd3%u7801%u9090%u6858%ucbd3%u7801%u9090%u6858%ucbd3%u7801%u9090%u90
90%u8190%u00c3%u0003%u8b00%u531b%u53ff%u0078%u0000%u00=a HTTP/1.0
...
Woomert and Frink looked at the screen, at each other, and exchanged a high-five salute, with Frink adding his "double twist with finger snaps" variation.
- "Woo-hoo! I called it right, Woomert. What do you think?"- "You did indeed, Frink, It looks like a modified version of a common worm, Code Red. The good news is that we're not dealing with a particularly sophisticated attacker, though: a Code Red infection attempt, which is what this is, is not the same thing as a Code Red DoS, which is just a network slam of a specific IP - and it only works against legacy operating systems, certainly nothing as modern as Linux - which is what this site runs. All these guys have going for them is bandwidth, and that's not particularly bad - and once the client blocks those IPs and notifies the relevant ISPs, it won't be an issue at all. In fact, there are analysis and response utilities that can track this sort of thing and do it automatically, and I'll recommend them to the client. Here - "
Woomert quickly fired off the results and his comments to the client by piping them into the "mail" program, and turned to Frink.- "...shall we? I have a Paglia e Fieno con Pollo e Funghi that should only take a few minutes to finish preparing, a tiramisu made to my own recipe for desert, and a really great '97 Rosso di Cerbaiona wine that should go well with it all. My girlfriend, the lovely Priority Interrupt, is going to join us."
- "Well, if you're sure that I won't be in the way..." - "Nonsense, Frink; we'd love your company."
After dinner, Frink lounged in the big armchair and Priority curled up in Woomert's lap and lit a huge Toscano cigar, which she used to produce beautuful double and sometimes triple rings of smoke. At Woomert's inquiring glance, she reached up and placed the cigar between his lips.
- "Aaah - luxury." Woomert leaned back and blew several rings that interlaced with Priority's. They smiled at each other. "So, Frink - questions? Answers? Guesses? Lay it on, my friend."Frink grinned at the two of them across the room.
- "Sure. I'm getting pretty good at reading those one-liners, though - I might need a little help, but I think I'm getting there. What was it you typed, now... ah, here it is - I copied it into my Zaurus:
OK, so - the `-wlne' switches enable warnings; read and print everything in `line mode', which strips EOL characters before and adds them back after; loops over the entire file one line at a time; and executes the code that follows. That's the easy part - I've been studying ``perldoc perlrun'' lately. Now, the code -
perl -wlne'/^(\S+)/;$h{$1}++}{$a=@a=values%h;map{$b+=$_}@a;print$b/$a' access.log
/^(\S+)/
is a regex that captures all non-space characters starting from the beginning of the line. If we look at some typical lines from `access.log' -127.0.0.1 - - [09/Mar/2003:22:14:46 -0500] "GET / HTTP/1.0" 200 50000 "http://localhost/" "Lynx/2.8.4rel.1 libwww-FM/2.14" webcache-01.segfl.ifl.net - - [01/Apr/2003:05:45:27 -0500] "GET / HTTP/1.0" "-" 200 5238
we'll see that it's going to catch the IP or the hostname, either of which is terminated by a space. Next, I see something you've done before:$h{$1}++
That's a frequency count, isn't it?"At Woomert's encouraging nod and smile, Frink went on.
- "OK. '$1' is a variable created by Perl which holds the first capture - that is, the contents of the first pair of parentheses in a regex. In this case, that's the IP. So, you use the IP as a key in the `%h' hash - and increment the value associated with that IP every time you see it. If it's a new IP, you get a new key.Next... um. Next, there's a closing brace all by itself... and I don't understandand what it does - or even why the code works. Shouldn't that fail with a syntax error?"
Woomert grinned."Normally, it would. However - go ahead and pull up ``perldoc perlrun'' again, and take a look at the entry for `-p':
# From ``perldoc perlrun'' while (<>) {
... # your program goes here
} continue {
print or die "-p destination: $!\n";
}
Note the ``your program goes here'' comment. What happens if you insert
a closing brace there?"
Frink concentrated on the code. Suddenly, his face lit up.
- "Oh! I see it, I see it! A closing brace would terminate the `while' statement... and an opening brace after it would create a block just past it. What you've done is get out of the `while' loop; everything after the curly brace only gets executed once. This is almost the same as using an `END{}' block. Wonderful! [2]All right, since we have that, the rest isn't too tough. Let's see:
$a=@a=values%h;All right, you extract the list of values - all the counts - from the hash and set `$a' to the number of values returned; that's what you get when you look at a list in a scalar context (it's a bit more complex than that, but that's the part that's important right now.) Next, you sum up all those values -
map{$b+=$_}@a;
The `map' function iterates over `@a' and increments `$b' by the value of each of the elements. Last but not least - print$b/$ayou print out the ratio of that sum over the count of the elements - thus dividing the total hits by the number of IPs. How's that?"
Woomert and Priority clapped and cheered as Frink turned pink and bowed, smiling.- "Thank you, thank you... I guess spending all that time studying under Woomert's direction is starting to pay off - thanks, Woomert! The rest of them are somewhat similar:
perl -wlne'/^(\S+)/;$h{$1}++}{print"$h{$_}\t$_"for sort{$h{$a}<=>$h{$b}}keys%h' access.log
The first part we already know - do a frequency count of the IPs. In the end block, however, you do something different; we'll parse it right to left, just as Woomert taught me:
sort{$h{$a}<=>$h{$b}}keys%h
OK - this time, you extract the keys, and... oh, I see. You want to sort the hash by value, but plain old ``for ( values %h ){ ... }'' won't work - there's no way to retrieve a key given a value, since values aren't necessarily unique. So, you change the `sort' routine - just as ``perldoc -f sort'' explains - to sort the keys based on the value. This is done by using `$a' and `$b' which are the variables that Perl uses to hold the elements that `sort' is currently comparing. In return, you get a list that's sorted by value and still allows you to look at keys - slick! Next, you take that list and print it with a bit of formatting:print"$h{$_}\t$"for ...
You loop over the list of returned keys with the "for" operator. The default variable in the loop, `$_', contains each key in turn, and `$h{$_}' return its associated value. You then print a tab and the key - which is the IP or the hostname. This gives us our list of IPs - and the associated number of hits.Last but not least, we have this:
Whew. It's a tough one. Let's see: the regex isn't too bad -
perl -lne'/^(\S+).*?"(.*?)"/;length$h{$1}>length$2or$h{$1}=$2}{print"@a"while@a=each%h' access.log
/^(\S+).*?"(.*?)"/
Woomert lazily extracted a laser pointer from his shirt pocket and pointed.
- "I assume you mean this?length$h{$1}>length$2or$h{$1}=$2
What I needed to do here is save the longest string as the value. In order to do that, I had to compare the current value for a given IP with the next value for that IP that came along. However, the initial value for a new key is undefined - and Perl would give us an error message if we compared something to an `undef'. That, as well as the interpolation of "@a" at the end are both things that would cause Perl to generate a non-fatal warning - so I turned off the warnings by skipping the `-w' switch, something you should not do unless you understand all the effects of doing so (read ``perldoc perllexwarn'' for more.) The method itself is fairly simple: I compare the length of the value currently assigned to the key; if it is greater, I replace the old value with the current one (contained in `$2'). Note that I'm using the soft `or' operator: a logical `or' (||) would not work here, since it would bind too tightly to the surrounding elements.Can you do the rest?"
Frink nodded.- "Yes; it looks fairly easy.
print"@a"while@a=each%hI've seen you do this before... oh yes. It's a ``while each'' loop that retrieves a key-value pair from a hash; you're assigning them to an array and printing the array. Since you've interpolated it by using double quotes around the array name, you'll get a space between the elements - which makes it nicely readable. All together, this prints out our hash - in more-or-less random order, but we don't really care since we just want to see what's in it. Right?"
- "Very good, Frink; you've done very well. I'll be relying on you to provide some backup in our further adventures, then. Are you ready for it?"- "I... I hope so, Woomert." Frink looked up, proud as can be. "I believe so. I'll certainly do my best. I'll head off for home then, and leave you two alone. Have a great night."
As the door closed behind the inordinately proud Frink, Priority smiled at Woomert.- "You've made Frink's week, you know. That's quite a compliment."
- "He deserves it; he's learned quite a lot. I'm very pleased with him, and quite proud of him. And now, Priority," Woomert's laser pointer fired a beam at the stereo, which softly began to play an Ella Fitzgerald/Luis Armstrong rendition of ``Can Anyone Explain'', "we have far more important things to discuss than Frink or programming..."
Ben is a Contributing Editor for Linux Gazette and a member of The Answer Gang.
Ben's subsequent experiences include creating software in nearly a dozen
languages, network and database maintenance during the approach of a hurricane,
and writing articles for publications ranging from sailing magazines to
technological journals. Having recently completed a seven-year
Atlantic/Caribbean cruise under sail, he is currently docked in Baltimore, MD,
where he works as a technical instructor for Sun Microsystems.
Ben has been working with Linux since 1997, and credits it with his complete
loss of interest in waging nuclear warfare on parts of the Pacific Northwest.
 Ben was born in Moscow, Russia in 1962. He became interested in
electricity at age six--promptly demonstrating it by sticking a fork into
a socket and starting a fire--and has been falling down technological mineshafts
ever since. He has been working with computers since the Elder Days, when
they had to be built by soldering parts onto printed circuit boards and
programs had to fit into 4k of memory. He would gladly pay good money to any
psychologist who can cure him of the resulting nightmares.
Ben was born in Moscow, Russia in 1962. He became interested in
electricity at age six--promptly demonstrating it by sticking a fork into
a socket and starting a fire--and has been falling down technological mineshafts
ever since. He has been working with computers since the Elder Days, when
they had to be built by soldering parts onto printed circuit boards and
programs had to fit into 4k of memory. He would gladly pay good money to any
psychologist who can cure him of the resulting nightmares.
|
...making Linux just a little more fun! |
By Dustin Puryear |
| Title: | Perl for System Administration |
|---|---|
| Author: | David N Blank-Edelman |
| Publisher: | O'Reilly & Associates |
| Published: | July 2000 |
| Cost: | $34.95 |
Perl is a great programming language. While not the most aesthetically pleasing or the most rigorously structured, the language is powerful, flexible, and very close to being ubiquitous in the networking world. And for system administrators Perl fulfills a very important need as a tool language: The ability to work, and to work well, under both Windows and UNIX.
There are a lot of useful things that you can do with Perl, including managing users, adjusting quotas, and monitoring log files and the Event Log. In Windows you can do much of this in Windows Scripting Host (WSH), and UNIX users have long had other tools to do these jobs. However, Perl is a major player these days in managing mid-size to large systems, and with Perl there comes a higher level of integration in managing disparate systems.
In 2000 O'Reilly & Associates published "Perl for System Administration," by David N Blank-Edelman. This book, despite having been published two years ago, is still an excellent resource for Windows and UNIX system administrators alike. Better yet, if you are managing a mixed environment, Blank-Edelman's book is even more valuable because of the emphasis on using Perl as a cross-platform tool to help manage UNIX, Windows, and even the Mac.
"Perl for System Administrators," weighing in at 418 pages, includes a very wide range of topics. The ten chapters, "Introduction," "Filesystems," "User Accounts," "User Activity," "TCP/IP Name Services," "Directory Services," "SQL Database Administration," "Electronic Mail," "Log Files," and "Security and Network Monitoring," form a solid foundation for building solutions across systems.
Now what is truly interesting about this book is the focus on supplying either cross-platform solutions, or if that doesn't directly apply, of ensuring that both Windows and UNIX needs are addressed in some depth for each given topic. For example, when discussing log monitoring in Chapter 9, "Log Files," Blank-Edelman discusses how to filter through both Windows Event Log and UNIX log entries. Using the information presented in this chapter you can begin to create a cross-platform log monitoring application for your own network.
Alas, the focus on the cross-platform aspects of Perl may be an issue for readers that want either a Windows- or UNIX- only focus. However, I would argue that it is this very lack of focus on either platform that brings "Perl for System Administration" to the next level. (If you are looking to learn how to use Perl under Windows then "Learning Perl on Win32 Systems," also by O'Reilly, would be a good choice.) Essentially, by the end of the book you will have learned to consider various administrative tasks at a higher-level so that you can address either Windows or UNIX systems with a cohesive solution, and in the end this kind of high-level design gives you a more robust and scalable solution.
As far as caveats, "Perl for System Administration" does require that you are an intermediate Perl user. The book is in no way an introduction to Perl, so be prepared to read an introductory text if you are new to Perl before reading this book. Also, I did find that some of the Perl modules mentioned in the book, and that you must install on your own systems, are difficult to find despite the pointers presented at the end of each chapter.
If you are responsible for managing more than a few servers or workstations then I suggest you check this book out. While you may not use all of the techniques and solutions presented in the book-for example, not everyone will have SQL servers to manage-there is more than enough information presented here to keep you thinking of your own custom Perl solutions far into the future.
![[BIO]](../gx/2002/note.png) Dustin Puryear, a respected authority on Windows
and UNIX systems, is founder and Principle Consultant of Puryear
Information Technology. In addition to consulting in the information
technology industry, Dustin is a conference speaker; has written
articles about numerous technology issues; and authored "Integrate
Linux Solutions into Your Windows Network," which focuses on
integrating Linux-based solutions in Windows environments.
Dustin Puryear, a respected authority on Windows
and UNIX systems, is founder and Principle Consultant of Puryear
Information Technology. In addition to consulting in the information
technology industry, Dustin is a conference speaker; has written
articles about numerous technology issues; and authored "Integrate
Linux Solutions into Your Windows Network," which focuses on
integrating Linux-based solutions in Windows environments.
|
...making Linux just a little more fun! |
By Raghu J Menon |
The setjmp/longjmp set of macros implemented in the C programming language provide the perfect platform to perform complex flow-control, but make sure that you have gained adequate knowledge about them, before you actually use them, or else your programs could become so complex that it would be impossible to discern them.
What do they do?
The setjmp function saves the state of a program. The state of a program to be precise are the values of sp (stack pointer), fp (frame pointer), pc (program counter). A program state is completely defined by these set of registers and the contents of the memory, which includes the heap and the stack. The next obvious question would be, why do i need to save the state for? Well simple to restore it later through longjmp. So these functions hunt in pairs i.e. setjmp saves the state, longjmp restores it.
The syntax is quite simple. setjmp stores the state of the program in a variable of type jmp_buf (defined in the header file setjmp.h). Always include the header file while working with these functions.
int setjmp (jmp_buf env);
int longjmp(jmp_buf env , int val);
The longjmp function restores the state of the program that is stored in env. The purpose of the parameter val will be explained later. So what does all this add upto? Simply that the longjmp function never returns (another one after exec). Before encountering a longjmp there has to be a setjmp which saves the state in env and returns a value 0. When you encounter longjmp next the state stored in env is restored and the program execution resumes at the instruction after setjmp. It is as though the longjmp returned through setjmp. This return should yield a value though and that value is what is specified through the parameter val.
i = setjmp (env);//Stores the state in env and returns 0
........... //Resume execution
at this point after the longjmp call as though the setjmp call
....... //returned.
longjmp(env,val)
As a last point, try printing the value of i. You would get 2 values, the first one is that obtained when setjmp saves the state and will be 0 always. The second one will be the value that you pass to longjmp through the val parameter. So the code after setjmp seems to get executed more than once. That calls for some exploration. We therefore have our first code and an interesting one too. if-else.c
Compile and run it. I hope you noticed it, both the if and else part of the condition are executed! Now, that is not how if-else condition is supposed to work. Looks like fork() (parent executing the if part and child executing the else or vice-versa). Well in fork we have two different threads of execution, that is not the case here. The setjmp call saves the state in env and returns 0. The if condition evaluates to true and you get the first message. Now later in the code when longjmp is executed the state is restored and you return to the statement following setjmp with a return value 2.
This return value is specified in the longjmp call. Now you see why the if condition failed and the else was executed. In addition the program showed disparity by not executing the last line. Well as i said earlier longjmp never returns and so it is quite obvious why the last line is not executed. If you take out the exit statement the code falls into a never ending loop alternating between the else part and the longjmp call.
As programmers you might have written code by dividing it into functions or subroutines (If not learn the art of functional programming. I started off by writing a C program as one big main function, gradually though i was able to split my program into functions. Why? It is easier to debug, that's why.). In implementing your program as functions there are bound to be function calls that are nested, that have pretty complex flow as well. Whenever an error occurs you need to find the function that caused it. This way it is easier to debug the program. The code below illustrates the use of setjmp/longjmp pair in debugging such programs. nest.c
Well the program does not do anything useful other than serve the purpose of illustrating graceful error handling. The code defines 4 functions, each one of them apart from accepting specified number of integer parameters, also has env as its parameter. The env holds the state of the program saved by the setjmp call in the main function. The failure in executing each of the function is specified in the if condition. Compile the program and execute it. Enter the following sets of values for l, m, n.
Enter values (integer) for l m and n please
1
4
7
The functions executed normally
Enter values (integer) for l m and n please
0
0
0
There is an error in function 1 exiting..
Enter values (integer) for l m and n please
1
1
2
There is an error in function 2 exiting..
Enter values (integer) for l m and n please
0
1
2
There is an error in function 3 exiting..
Enter values (integer) for l m and n please
1
2
3
There is an error in function 4 exiting..
Well that was useful i suppose. The error message could tell you where the error occurred. Let us trace the code. The setjmp in the main function saves the state of the program and returns 0. The if condition equates to false and therefore is not executed. The next statement calls the function fun1 with parameters env, l, m, n, fun1 in turn calls fun2 and so on. Whenever an error occurs in any of these functions a longjmp is executed, the val parameter being the function number where the longjmp was executed. The program returns to the main function (to the statement after setjmp) whenever a longjmp is executed. The value in s now is either 1, 2, 3, 4, depending on where the longjmp was made from. The if condition now equates to truth value and therefore an appropriate error message is flagged indicating the function in which the error occurred. If no error occurred during the execution of the program the functions return normally and the last statement of the main function is executed. Why don't i just use the goto statement to make a jump during an error? Try compiling the code below goto.c. The error flagged is because goto can be used only for local jumps. The jumps in the previous program made by longjmp where non-local ones, goto searches for local labels and hence cannot make non-local jumps.
There is a subtle bug in setjmp/longjmp, not in its implementation, but in the way we use it. Most of us are quite unaware and rightly so of the stack state when we write a program. It is when there is an error we try and trace it by inspecting the stack (through gdb). Whenever there is a function call the stack is manipulated. First the arguments to the called function are pushed in the reverse order. Next the JSR is called to push the return address (pc) and then the fp, fp and sp are then emptied to make a new stack frame for the called function. The called function immediately on entry creates space on the stack for the local variables that might have been declared in the function. Now that you have an idea of the stack structure, try running the code below seg.c. It compiles fine, but alas it fails to run completely and faults. Could you find the reason?
Let us trace the code. The main function calls me_first with 2 arguments, the arguments are pushed onto the stack env followed by the string "IC-Labs", the JSR then pushes the pc and fp values on the stack. On entry the function creates a local variable i on the stack. This is followed by a call to the setjmp function which saves the current state, that of me_first function. The local variable now contains the value 0, value returned by setjmp. After returning from me_first the stack is returned to the original state, one in which it left the main function. The i_follow function is called next with a value 3 and the env variable. The stack is modified as above (when me_first was called). In the function the state stored in env is restored by longjmp. The values in the stack remain the same i.e. as they where during the execution of function i_follow . The state though is that of function me_first. The stack frame of this state has a variable of type (char * ) which previously had a string "IC-Labs". Now after the state has been restored the value that variable s holds is 3 (the value that i_follow was passed from the main). As a result of the longjmp the statement following setjmp in me_first is executed. In executing the statement after setjmp (printf), there is an illegal memory access since in trying to print out s the program tries to find a string at memory location 0x3 which causes a memory protection error and causes the program to fault. This bug is very subtle and often goes unnoticed, this is because the stack frame of both the functions look almost the same. In cases were the stack frames are the same there is no such error. Try replacing the argument "char *" with one of type int, and rerun it. Did it fault?
One of the beauties of these functions is that you can longjmp from a signal handler and return to your program and catch those signals again. Check out the program below sig.c
The main function installs a signal handler using the signal system call, parameters are the signo(SIGALRM), which indicates the signal for which you are setting up the handler and the handler routine which is executed when the signal occurs. The alarm call sends the SIGALRM signal to the program every second. The alarm_handler basically longjmps out after 8 seconds have passed.
![[BIO]](../gx/2002/note.png) I am almost through with my graduate studies in computer
science and engineering. I hail from Trichur (a small town in god's own country,
Kerala). Any constructive criticism with regards to the style and content are
welcome. Please feel free to contact me via e-mail.
I am almost through with my graduate studies in computer
science and engineering. I hail from Trichur (a small town in god's own country,
Kerala). Any constructive criticism with regards to the style and content are
welcome. Please feel free to contact me via e-mail.
|
...making Linux just a little more fun! |
By Alan Ward |
The CUPS printing system is what its name says: a Common Unix Printing System. It is aimed at providing a common printing interface across a local network, masking differences between the printing system on each computer. While I am not sure that such a system is really needed in a purely Linux environment where the standard Berkely LPD provides this functionality, CUPS does provide interactivity with SMB and Windows printers. CUPS also allows dynamic printer detection and grouping.
CUPS is licenced under GPL by a company called Easy Software Products. Besides providing CUPS itself as free software, it also provides commercial addons and support.
You can get it from www.cups.org, or as a RPM package for most distributions (seen it for Mandrake, RedHat and SuSE).
How does it work?
CUPS can be seen as a replacement of the LPD printing system. It replaces the lpr command with its own, and the LPD printer drivers with its own versions. However, it is very similar to LPD in that it is based on PostScript as its underlying language for page description. Linux (and Unix) programs won't know the difference between CUPS and LPD.
It contains a list of printer drivers that include most printers with parallel port, USB and even serial connections. Note serial - connecting a printer with a null-modem serial line is slow and more difficult to set up than a parallel line, but it is sufficient for a matrix printer -- for bulk printing or multiple copies -- and makes an easy way to build a print server from a pile of older hardware. A hint to schools!
Dynamic printer detection
CUPS has a characteristic of Windows systems that is not very common in the Unix world: it broadcasts the printers available on the local computer to all other computers on the network. In this way, every computer on the local IP segment gets to know in real time which printers are available and what their status is.
Naturally, this is -- unlike Windows :-) -- configurable. You can tell CUPS (in the cupsd.conf configuration file) if and where to broadcast to, and specify how often the information is refreshed.
Grouping printers
A printer group -- called a class by CUPS -- is a group of printers that appears as a single printer to user programs. For example, you could create a group called ColorPrinters, including all your color printers. The user could then tell his program to print on printer ColorPrinters, and the output would be on one of these printers. Which one would depend on user rights or which printer is currently available.
The fact that a printer is a member of a group does not mean, in itself, that users cannot use that printer directly. However at CUPS access control level, you can make the printers reject jobs - while groups accept them. The end result is that users can use printer groups, not printers. It depends a bit on the policy on printer use you intend to implement.
I have a workshop with five computers under Linux, all running CUPS. When changing a printer on one of them, I:
through the CUPS web interface in under 30 secs. That is all the configuration required - the other computers get their default printing routes updated in another 30 secs. Under 1 minute for the whole change: less time than a laser printer takes to warm up.
I like to provide, in my school network:
Most of these printers hang off Windows boxes and would be directly available for other computers under Windows. However, by providing them through CUPS on a central bridge/router, I:
Integrating with Windows
To use a Windows printer under Linux or the other way round, you will need to have a Samba server working. Set this up and test it before going on (as a normal user, try viewing your home directory on the Linux computer from a Windows box). Remember to turn password encyptation on in /etc/samba/smb.conf if you are using Windows 98 or a more recent version.
CUPS can use printers shared from computers under Windows, and network printers using the SMB protocol. You configure a "Windows printer using Samba". Basically, all you have to tell CUPS is the address of the printer, as in: smb://server/printer.
Windows can use a CUPS printer shared by Samba. Proceed in the normal way to share your printers with Samba: i.e. do not do anything. Your printers are generally shared by defect. If this is not the case, edit smb.conf to create the necessary share. All the Samba share options are appliable. This is because Samba treats a CUPS printer in the same way as a LPD printer.
Network printers
Network printers -- i.e. a printer with a network interface, that doesn't need a host computer to be made available to the network -- can use any of a variety of protocols:
In the first two cases, proceed as with a printer hosted by a computer. In the third, you are probably at a dead end. This happened to me with a Lexmark: I ended up sharing it from a Windows box.
Configuration
There are two ways of configurating CUPS. One is editing the configuration file /etc/cups/cupsd.conf. The other is a classical web-based interface you can access at port 631. This is very similar to the web-based configuration of many network-capable printers, and should be intuitive for all.
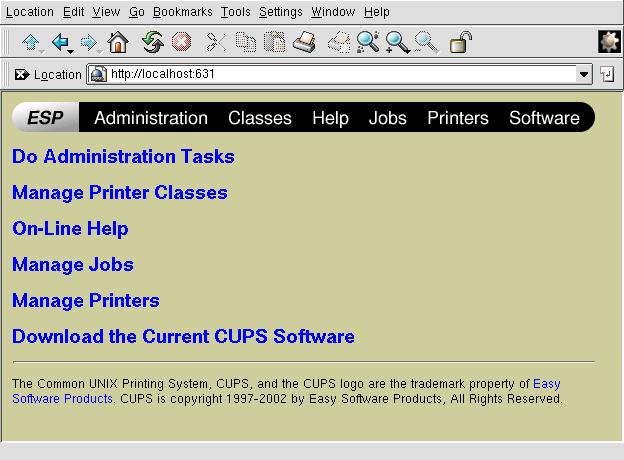
Generally, you can access the web interface only from the localhost interface, not from other computers. However, you can change this by changing the following lines in the configuration file cupsd.conf, and restarting CUPS:
<Location /> # this location is the main screen
Order Deny, Allow
Deny From All
Allow From 127.0.0.1 # allow configuration from local host
Allow From 192.168.1.* # allow configuration from any machine
# on the 192.168.1.0/24 subnet
Allow From mybox.mydomain # this is my desktop on another segment
</Location>
You can also specify one by one which menu items (called Locations in CUPS terms) are accessible from any particular IP address. This doesn't mean that other computers will not be able to connect to the server - just that they won't be able to access contents.
If your Linux box is acting both as a print server and a bridge between two or more IP segments, you can also specify on which network interfaces it will listen for requests:
Listen 127.0.0.1:631 # Should already be there Listen servename:631 # Add your server name here Listen 192.168.1.1:631 # You can also use your IP address
In the above example, the web interface will be visible through my eth0 interface with IP address 192.168.1.1, but not through the eth1 interface with IP address 172.16.0.1 .
Though user identification is required through basic login/password authentication, note that you can use SSL to connect to the web interface through the https secure protocol. This is also relatively easy to configure in the cupsd.conf file.
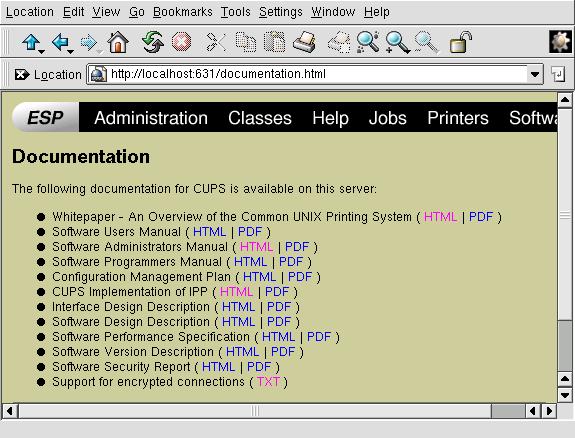
The web interface has a comprehensive help system with plenty of documentation about what CUPS is and how to configure it.
PS. Should anybody want to translate this article: I wrote it in the spirit of the GPL software licence. i.e. you are free (and indeed encouraged) to copy, post and translate it -- but please, PLEASE, send me notice by email! I like to keep track of translations -- it's good for the curriculum :-)
![[BIO]](../gx/2002/note.png) Alan teaches CS in Andorra at high-school and university levels. His hobbies
include science photography (both digital and traditional), trekking, rock and
processor collecting.
Alan teaches CS in Andorra at high-school and university levels. His hobbies
include science photography (both digital and traditional), trekking, rock and
processor collecting.
|
...making Linux just a little more fun! |
By Nick Weber |
Introduction
Installation
Running
Example 1: Networking
Example 2: System Calls
Example 3: Device Drivers
Example 4: SysV IPC
Code
References
The first step to get TUN/TAP is to install uml_utilities. This can be obtained from the UML website. To install the utilities untar the file, cd into the created directory and type 'make install'. This will install five programs into /usr/bin with uml_net being the one that we are interested in. uml_net will help do the setup so that the host and UML can communicate. The only drawback of this method is that uml_net is a setuid program and can be a possible security vulnerability. The setup that the uml_net program does can also be done on the host machine as the root user. This will be covered in a later addition.
For this example we will setup the host with an ip of 10.0.0.1 and the UML with 10.0.0.2. On the host machine assign the ip address to the eth0 interface with 'ifconfig eth0 10.0.0.1'. Now we boot the the UML machine with the following command './linux eth0=tuntap,,,10.0.0.1'. There are four paramaters that can be specified for eth0, but we are interested in the first and last one for now. The first one tells UML which transport to use and the last paramter specifies the ip of the host machine. A point of confusion for many is the last paramter. This is the ip of the host machine and not what you want the ip of the UML to be. After booting login and run 'ifconfig eth0 10.0.0.2' on the UML machine. Now you should be able to ping, ssh, ftp, etc to the host machine from UML and vice versa.
You will need to make changes to three files in the UML kernel directory. Starting from the UMLkernel directory they are include/asm/arch/unistd.h, arch/um/kernel/sys_call_table.c, arch/um/kernel/Makefile. The code for the system call will go in the arch/um/kernel directory. Using the code from code section as an example do the following:
Shared Memory
Shared memory allows you to map unused memory to be used by multiple processes.
There are four functions that are used to set up and use a shared memory
segment. They are: shmget(), shmat(), shmdt(), shmctl(). Since these functions
are implemented through system calls we can expect to find the underlying
system call of: sys_shmget(), sys_shmat(), sys_shmdt(), sys_shmctl() for
each of the functions respectively. Shared memory in UML is done the same
as you would for the host kernel. Check out shrmem1_sysV.c and shrmem2_sysV.c
for the source code of two programs using a segment of shared memory. Compile
each program with gcc, start shrmem2_sysV in the background then run shrmem1_sysV.
Message Passing
Another way to share data between programs is throught the use of the message
passing API. Like shared memory, the message passing API also has four functions
with underlying system calls. The user functions are msgget(), msgsnd(),
msgrcv(), and msgctl(), while the system calls are sys_msgget(), sys_msgsnd(),
sys_msgrcv(), and sys_msgctl. For an example of message passing compile
the two source files recvmsg_sysV.c and sendmsg_sysV.c. Start recvmsg_sysV
in the background then run sendmsg_sysV to see message passing in action.
#include <linux/kernel.h>
asmlinkage int sys_my_new_call(void) {
printk(KERN_ALERT "sys_my_new_call at your service\n");
return 0;
}
#include <sys/types.h>
#include <linux/unistd.h>
static inline _syscall0(int, my_new_call);
int main() {
int result;
result = my_new_call();
}
#define true 1
#define false 0
/* This will be the name we choose for our device. We will also
use this as a prefix on functions such as the entry points
appearing in the file_operations struct.
*/
#define DEV_NAME "pp"
static int Major;
/* These are prototypes for residents of the file_operations struct
*/
static ssize_t pp_read(struct file *, char *, size_t, loff_t *);
static ssize_t pp_write(struct file *, const char *, size_t, loff_t *);
static int pp_open(struct inode *, struct file *);
static int pp_close(struct inode *, struct file *);
/* This is the file_operations struct. The init_module function
will register this with the kernel so the kernel will know all
the entry points it contains.
*/
struct file_operations Fops = {
owner: THIS_MODULE,
read: pp_read,
write: pp_write,
open: pp_open,
release: pp_close,
};
/* The pp_probe function does nothing here, but reminds us that a
'real' driver may need to probe for hardware resources. These
resources might later be allocated in init_module.
*/
static int pp_probe(void){
return 0;
}
/* The pp_read function is a stub, but at least does a printk,
for tracing purposes, when it is called.
*/
static ssize_t pp_read(struct file *file, char *buff, size_t ctr, loff_t *woof) {
printk(KERN_ALERT "\npp_read active.\n");
return 0;
}
/* The pp_write function is a stub, but at least does a printk,
for tracing purposes, when it is called.
*/
static ssize_t pp_write(struct file *file, const char *buff, size_t ctr, loff_t *woof) {
printk(KERN_ALERT "\npp_write active.\n");
return 0;
}
/* The pp_open function does a printk for tracing purposes.
*/
static int pp_open(struct inode *inode, struct file *file) {
printk(KERN_ALERT "\nAn instance of %s has been opened.\n", DEV_NAME);
return 0;
}
/* The pp_close function does a printk for tracing purposes.
*/
static int pp_close(struct inode *inode, struct file *file) {
printk(KERN_ALERT "\nOne instance of %s has been closed.\n", DEV_NAME);
return 0;
}
/* Next we'll see that that init_module
* registers the file_operations struct so the kernel will know
about the entry points therein
* gets back a major number
* calls pp_probe, to look for hardware resources
Had hardware resources been found, they would need to be allocated
for use by this driver, probably within the scope of init_module.
*/
int init_module(void) {
Major = register_chrdev( 0, DEV_NAME, &Fops);
if (Major < 0) {
printk("Registration Failure!\n");
return Major;
}
if (pp_probe() < 0) {
unregister_chrdev(Major, DEV_NAME);
printk(KERN_ALERT "pp_probe() failure!\n");
return -1;
}
printk(KERN_ALERT "\nRegistered %s, at major number = %d.\n\n", DEV_NAME, Major);
printk("To use %s, you must create a device file.\n", DEV_NAME);
printk("If this has not already been done, then enter:\n");
printk(" mknod /dev/%s c %d 0\n\n", DEV_NAME, Major);
printk("Also set appropriate permissions for /dev/%s.\n\n", DEV_NAME);
return 0;
}
/* The cleanup_module function unregisters the driver and, in a
'real' driver would free up any resources allocated by
init_module.
*/
void cleanup_module(void) {
int ret;
ret = unregister_chrdev(Major, DEV_NAME);
if (ret < 0)
printk(KERN_ALERT "\nUnregistration problem where ret = %d\n\n", ret);
else
printk(KERN_ALERT "\nUnregistered %s, at major number = %d\n\n", DEV_NAME, Major);
}
#include <stdio.h>
#include <stdlib.h>
#include <fcntl.h>
#include <unistd.h>
#define DEVICE "/dev/pp"
int main() {
int ddfd = 0;
int ret = 0;
ddfd = open(DEVICE, O_RDWR);
if (ddfd < 0) {
printf("\nOpen of %s failed.\n", DEVICE);
exit(-1);
}
printf("\nOpen of %s succeeded.\n", DEVICE);
ret = close(ddfd);
if (ret < 0) {
printf("\nClosing %s failed.\n", DEVICE);
exit(-1);
}
printf("\n Close of %s succeeded.\n", DEVICE);
exit(0);
}
#include <unistd.h>
#include <stdlib.h>
#include <stdio.h>
#include <string.h>
#include <sys/types.h>
#include <sys/ipc.h>
#include <sys/shm.h>
#define MEM_SZ 4096
struct shared_use_st {
int writ_by_you;
char some_text[BUFSIZ];
};
int main() {
int run = 1;
void *shared_mem = (void *) 0;
struct shared_use_st *shared_stuff;
char buffer[BUFSIZ];
int shmid;
shmid = shmget( (key_t)1234, MEM_SZ, 0666 | IPC_CREAT);
if (shmid == -1) {
perror("shmget in shrmem1_sysV failed");
exit(EXIT_FAILURE);
}
shared_mem = shmat(shmid, (void *)0, 0);
if (shared_mem == (void *)-1) {
perror("shmat in shrmem1_sysV failed");
exit(EXIT_FAILURE);
}
printf("memory attached at %X\n", (int)shared_mem);
shared_stuff = (struct shared_use_st *)shared_mem;
while (run) {
while (shared_stuff->writ_by_you == 1) {
sleep(3);
printf("Waiting for client ...\n");
}
printf("Enter some text: ");
fgets(buffer, BUFSIZ, stdin);
strcpy(shared_stuff->some_text, buffer);
shared_stuff->writ_by_you = 1;
if (strncmp(buffer, "end", 3) == 0) {
run = 0;
}
}
if (shmdt(shared_mem) == -1) {
perror("shmdt in shrmem1_sysV failed");
exit(EXIT_FAILURE);
}
exit(EXIT_SUCCESS);
}
shrmem2_sysV.c
/* sysV IPC shared memory - read from shared memory
shrmem2_sysV.c
meant to be used with shrmem1_sysV:
start shrmem2_sysV in background,
then start shrmem1_sysV
*/
#include <unistd.h>
#include <stdlib.h>
#include <stdio.h>
#include <string.h>
#include <sys/types.h>
#include <sys/ipc.h>
#include <sys/shm.h>
#define MEM_SZ 4096
struct shared_use_st {
int writ_by_you;
char some_text[BUFSIZ];
};
int main() {
int run = 1;
void *shared_mem = (void *) 0;
struct shared_use_st *shared_stuff;
int shmid;
shmid = shmget( (key_t)1234, MEM_SZ, 0666 | IPC_CREAT);
if (shmid == -1) {
perror("shmget in shrmem2_sysV failed");
exit(EXIT_FAILURE);
}
shared_mem = shmat(shmid, (void *)0, 0);
if (shared_mem == (void *)-1) {
perror("shmat in shrmem2_sysV failed");
exit(EXIT_FAILURE);
}
printf("memory attached at %X\n", (int)shared_mem);
shared_stuff = (struct shared_use_st *)shared_mem;
shared_stuff->writ_by_you == 0;
while (run) {
if (shared_stuff->writ_by_you == 1) {
printf("You_wrote: %s", shared_stuff->some_text);
sleep(rand() % 4);
shared_stuff->writ_by_you = 0;
if (strncmp(shared_stuff->some_text, "end", 3) == 0) {
run = 0;
}
}
}
if (shmdt(shared_mem) == -1) {
perror("shmdt in shrmem2_sysV failed");
exit(EXIT_FAILURE);
}
if (shmctl(shmid, IPC_RMID, 0) == -1) {
perror("shmctl in shrmem2_sysV failed");
exit(EXIT_FAILURE);
}
exit(EXIT_SUCCESS);
}
#include <stdlib.h>
#include <stdio.h>
#include <string.h>
#include <sys/types.h>
#include <sys/ipc.h>
#include <sys/msg.h>
#define BUF 1024
struct my_msg_st {
long int my_msg_type;
char some_text[BUFSIZ];
};
int main() {
int run = 1;
struct my_msg_st some_data;
int msqid;
char buffer[BUF];
msqid = msgget( (key_t)1234, 0666 | IPC_CREAT);
if (msqid == -1) {
perror("msgget in sendmsg_sysV failed");
exit(EXIT_FAILURE);
}
while (run) {
printf("Enter some text:");
fgets(buffer, BUF, stdin);
some_data.my_msg_type = 1;
strcpy(some_data.some_text, buffer);
if (msgsnd(msqid, &some_data, BUF, 0) == -1) {
perror("msgsnd in sendmsg_sysV failed");
exit(EXIT_FAILURE);
}
if (strncmp(buffer, "end", 3) == 0) {
run = 0;
}
}
exit(EXIT_SUCCESS);
}
recmsg_sysV.c
/* sysV IPC message passing - receiver
recvmsg_sysV.c
meant to work with sendmsg_sysV:
start recvmsg_sysV in background,
then start sendmsg_sysV
*/
#include <stdlib.h>
#include <stdio.h>
#include <string.h>
#include <sys/types.h>
#include <sys/ipc.h>
#include <sys/msg.h>
struct my_msg_st {
long int my_msg_type;
char some_text[BUFSIZ];
};
int main() {
int run = 1;
struct my_msg_st some_data;
int msqid;
long int msg_to_recv = 1;
msqid = msgget( (key_t)1234, 0666 | IPC_CREAT);
if (msqid == -1) {
perror("msgget in recvmsg_sysV failed");
exit(EXIT_FAILURE);
}
while (run) {
if (msgrcv(msqid, &some_data, BUFSIZ, msg_to_recv, 0) == -1) {
perror("msgrcv in recvmsg_sysV failed");
exit(EXIT_FAILURE);
}
printf("You wrote: %s", some_data.some_text);
if (strncmp(some_data.some_text, "end", 3) == 0) {
run = 0;
}
}
if (msgctl(msqid, IPC_RMID, 0) == -1) {
perror("msgctl in recvmsg_sysV failed");
exit(EXIT_FAILURE);
}
exit(EXIT_SUCCESS);
}
Mathew, Neil, Richard Stones Beginning Linux Programming. 2nd ed. Wrox Press, Inc., September 1999.
Rubini, Alessandro, Jonathan Corbert. Linux Device Drivers. 2nd ed. O'Reilly Associates, Incorporated, July 2001.
Russell, Rusty. "User Mode Linux HOWTO". Online. Internet. 18, June 2002. Available: user-mode-linux.sourceforge.net/UserModeLinux-HOWTO.html.
![[BIO]](../gx/2002/note.png) I am currently pursuing a graduate degree in Computer Science from Eastern
Washington University in Cheney, Washington, USA.
I am currently pursuing a graduate degree in Computer Science from Eastern
Washington University in Cheney, Washington, USA.